analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
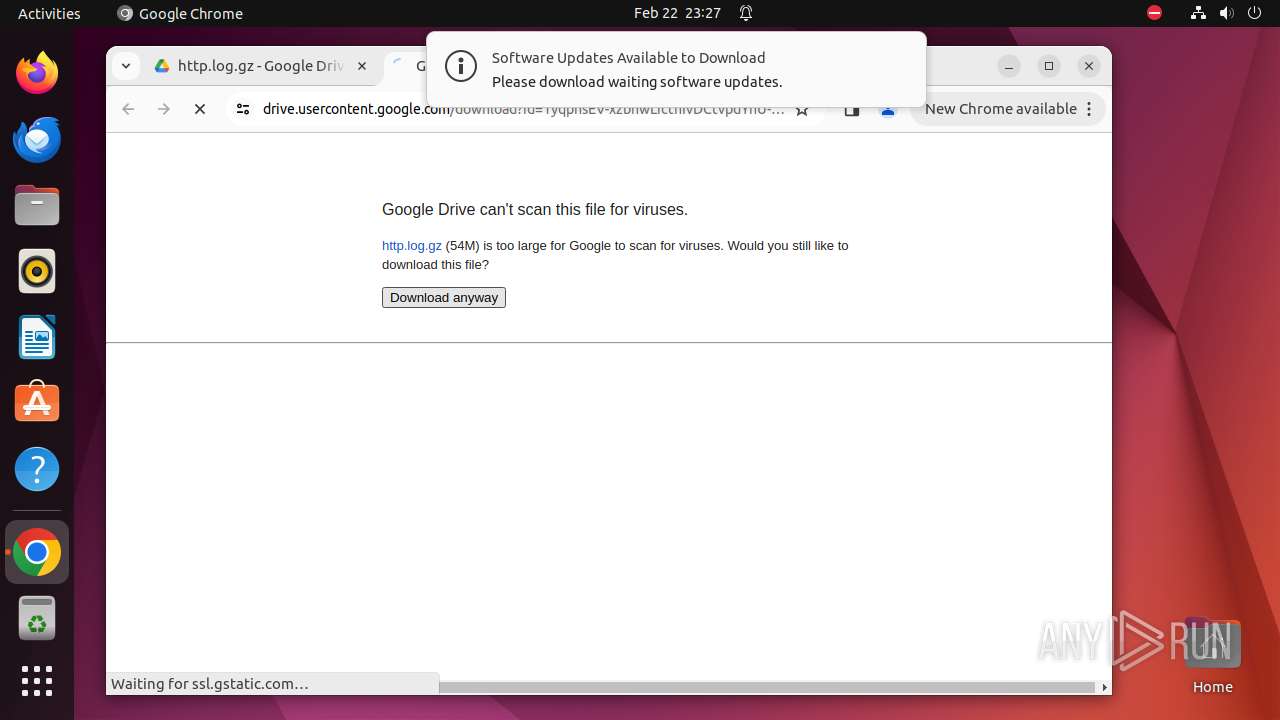
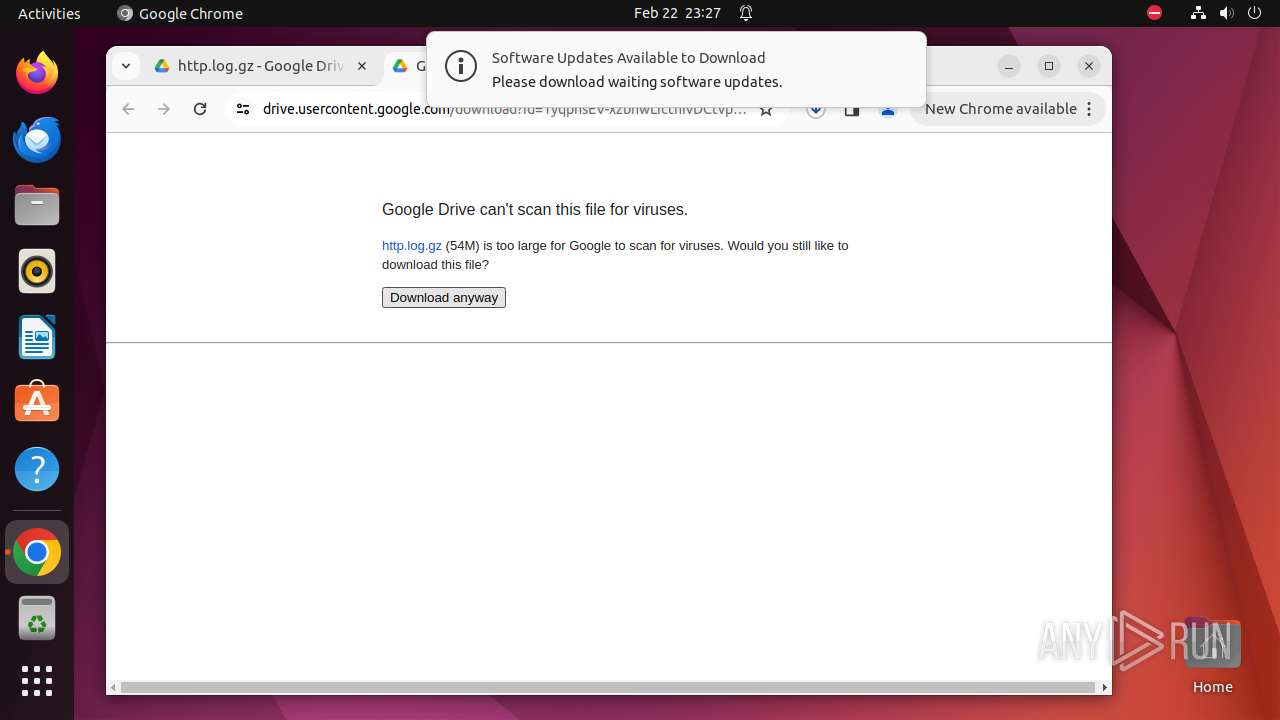
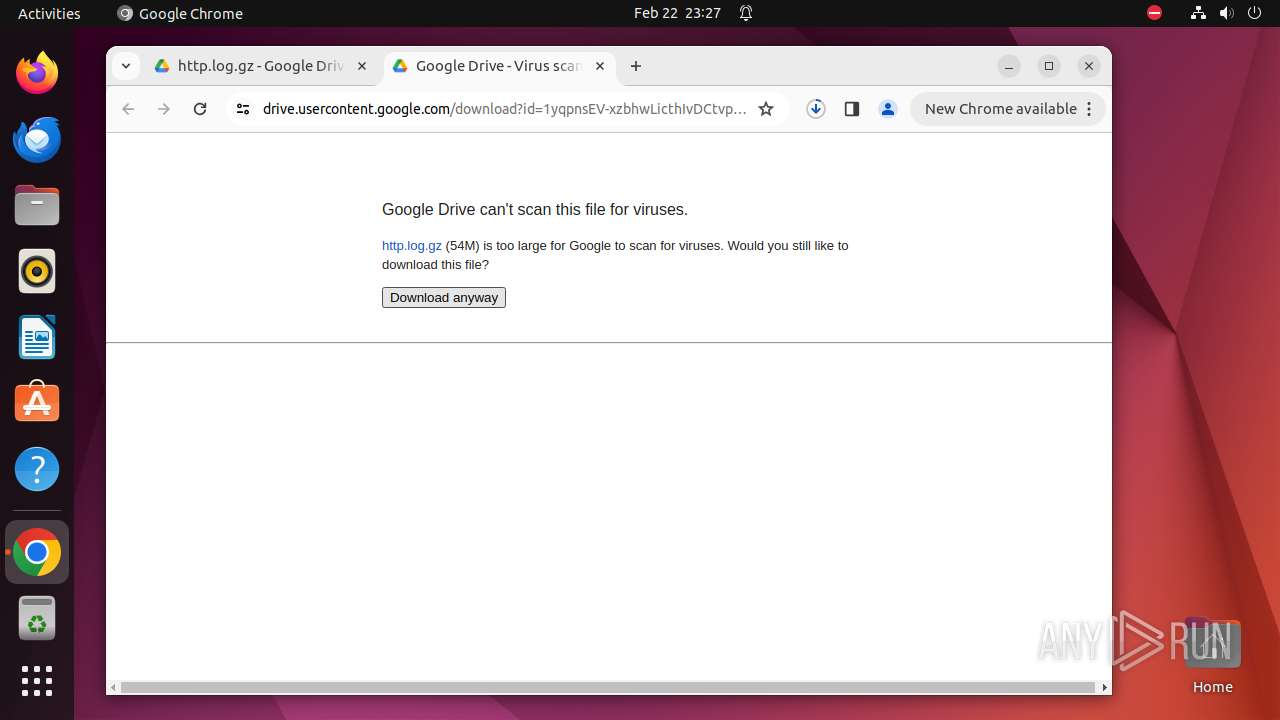
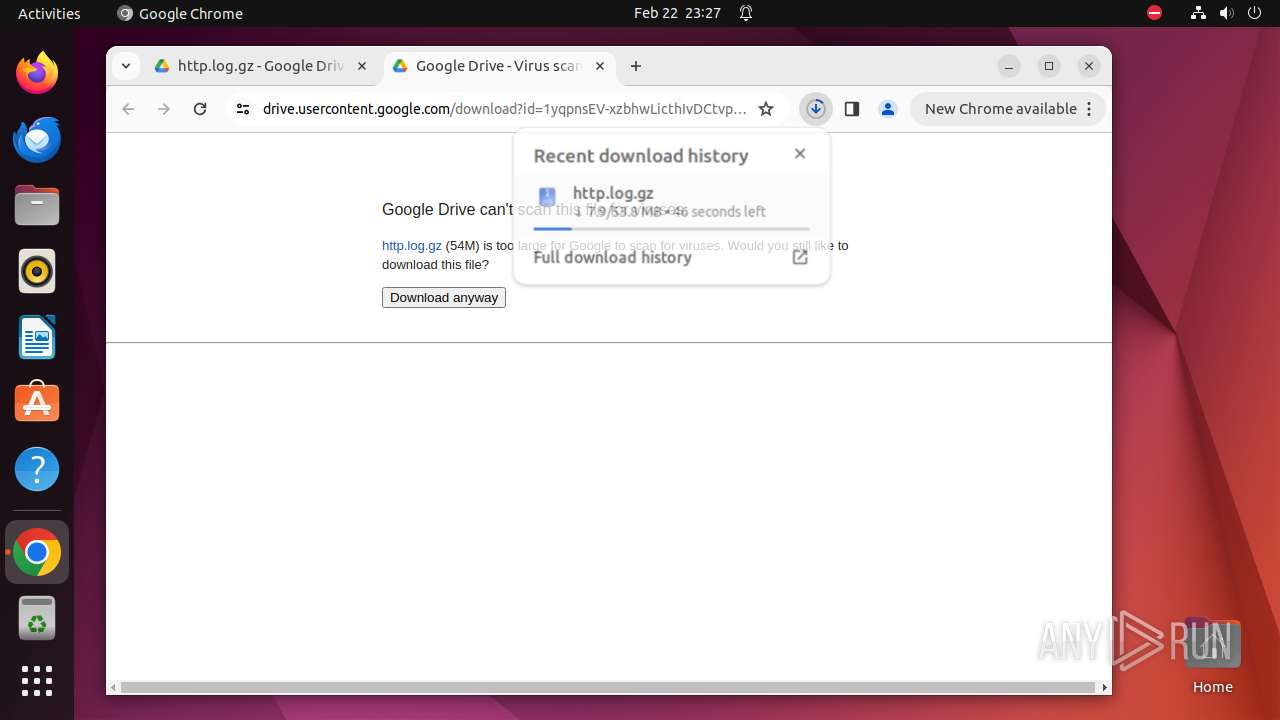
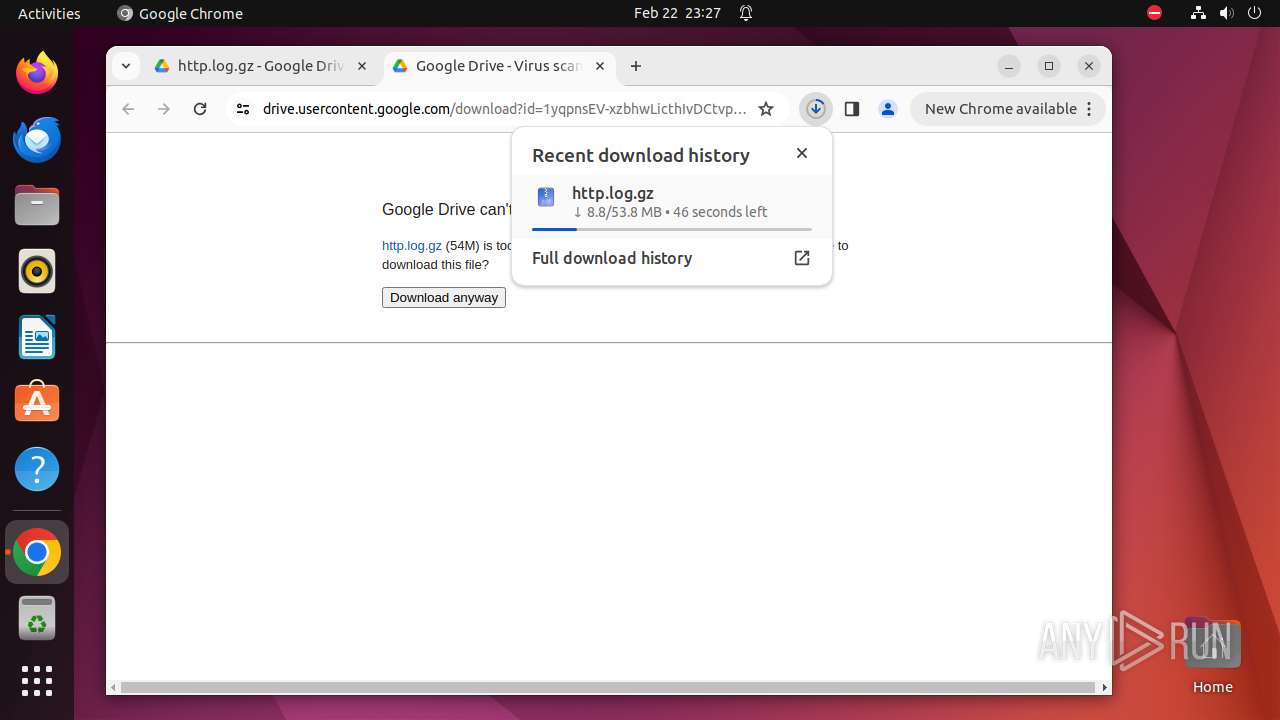
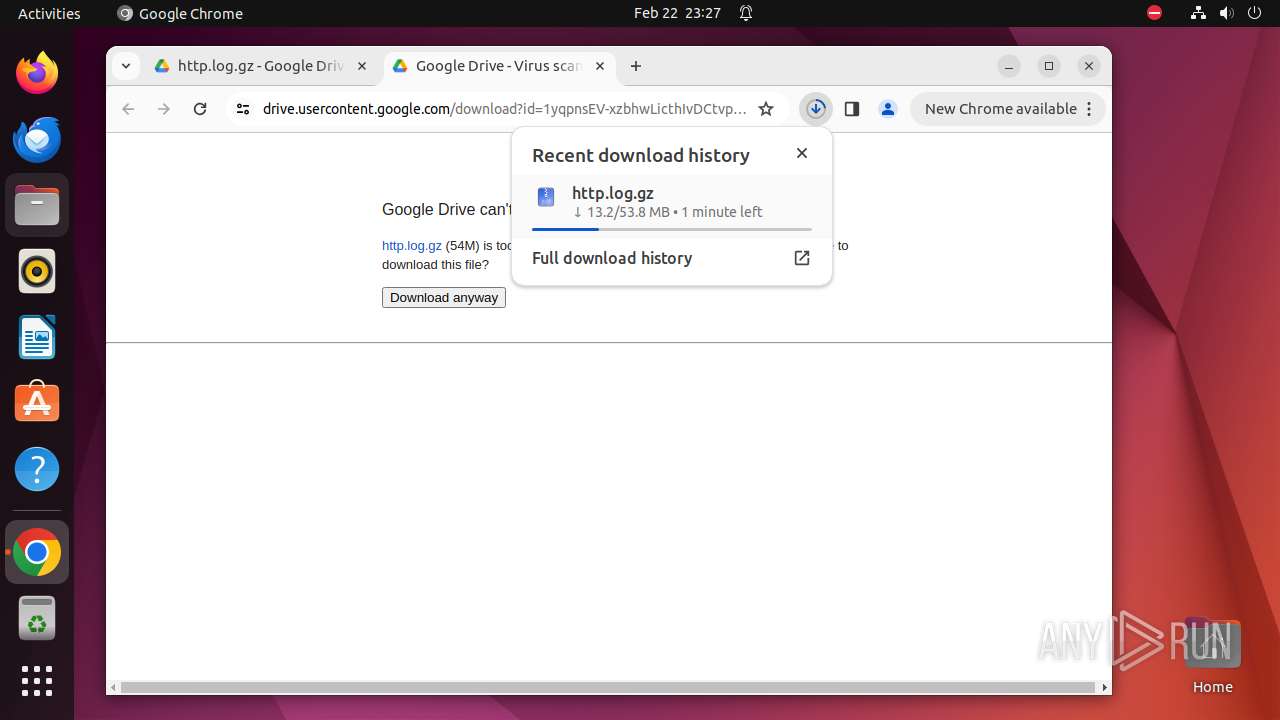
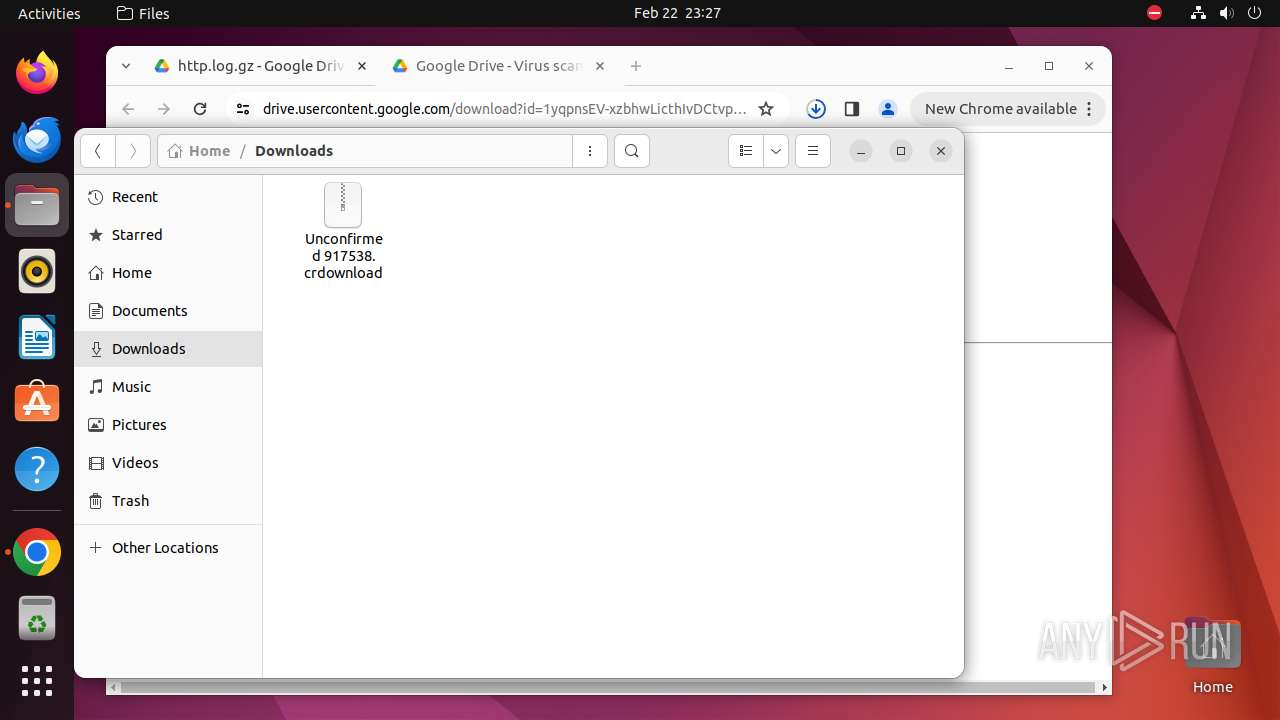
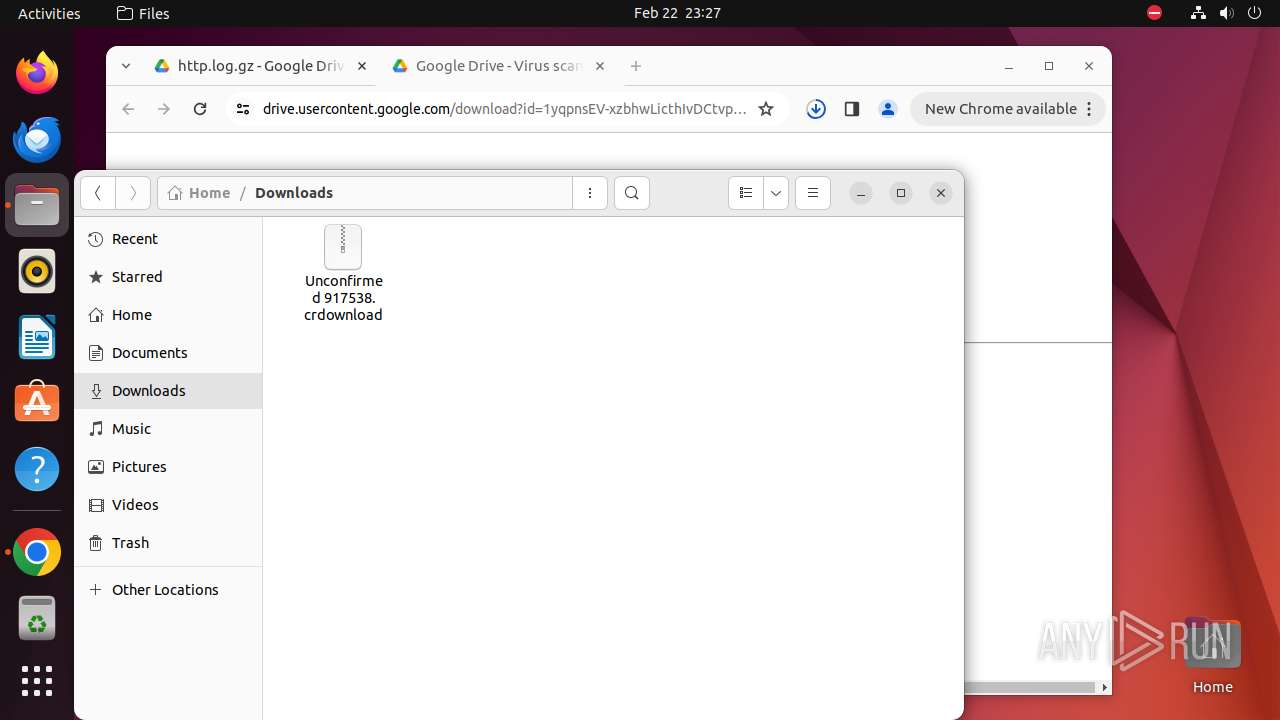
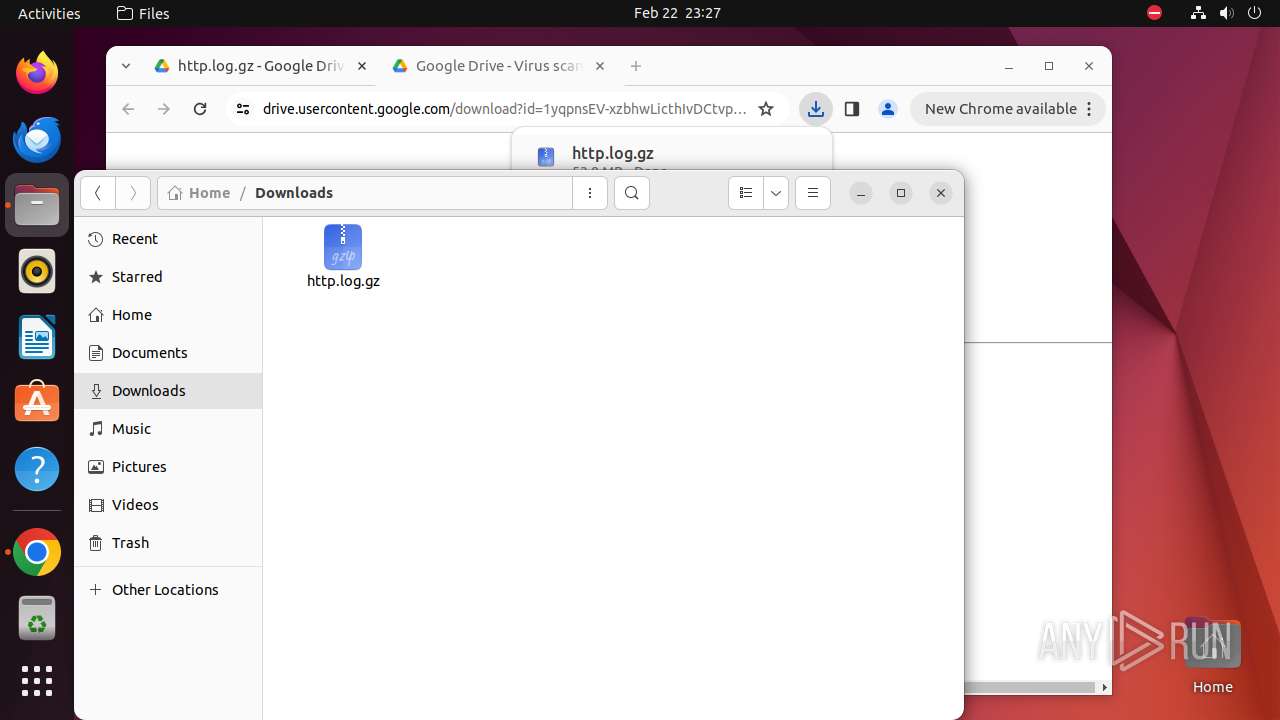
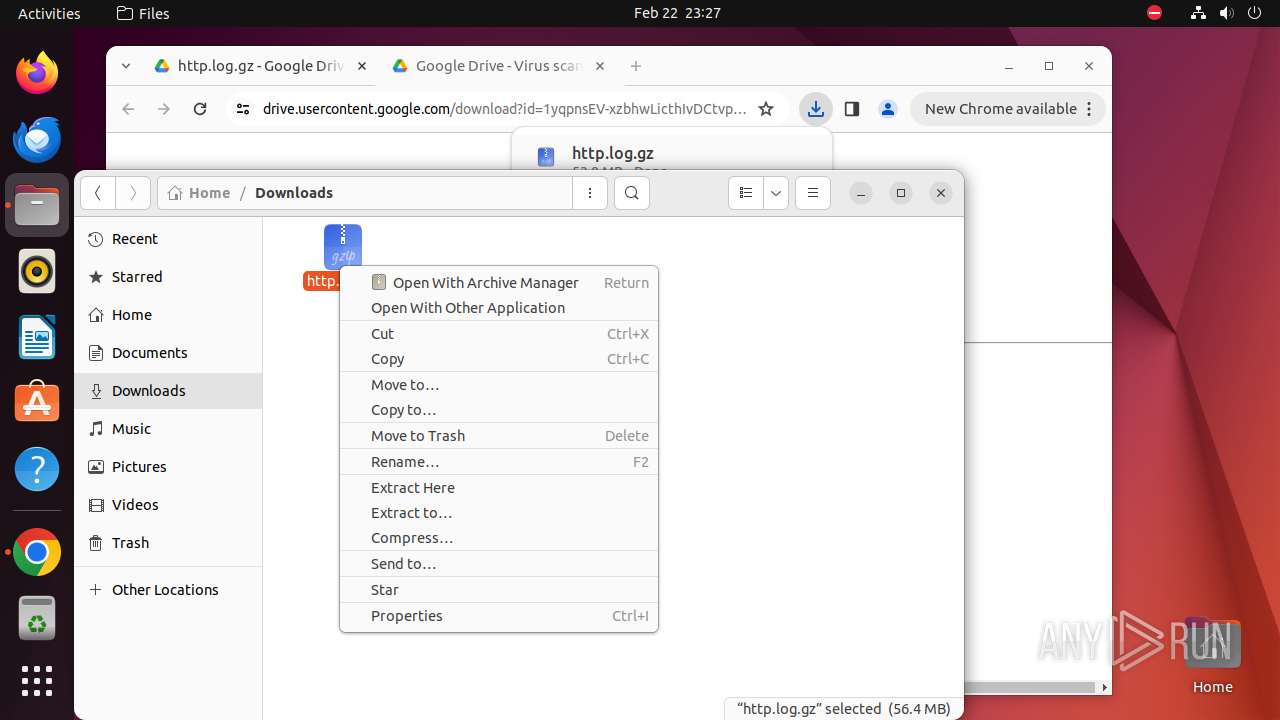
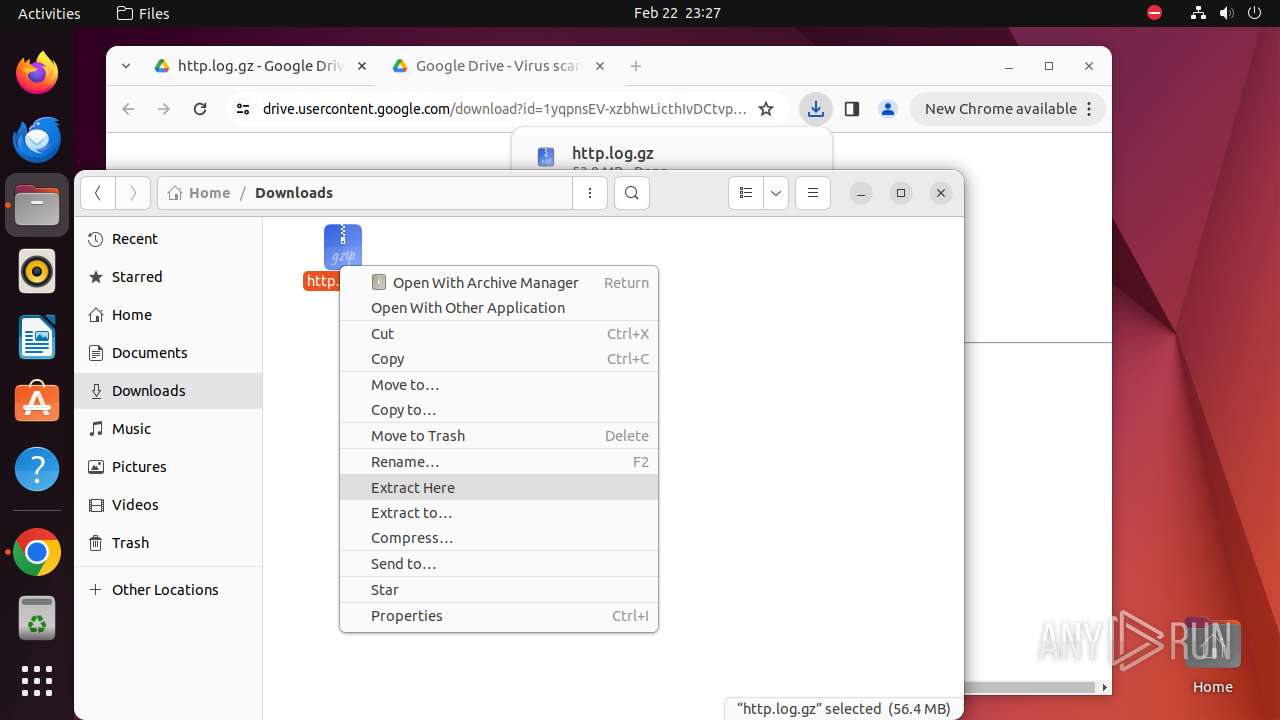
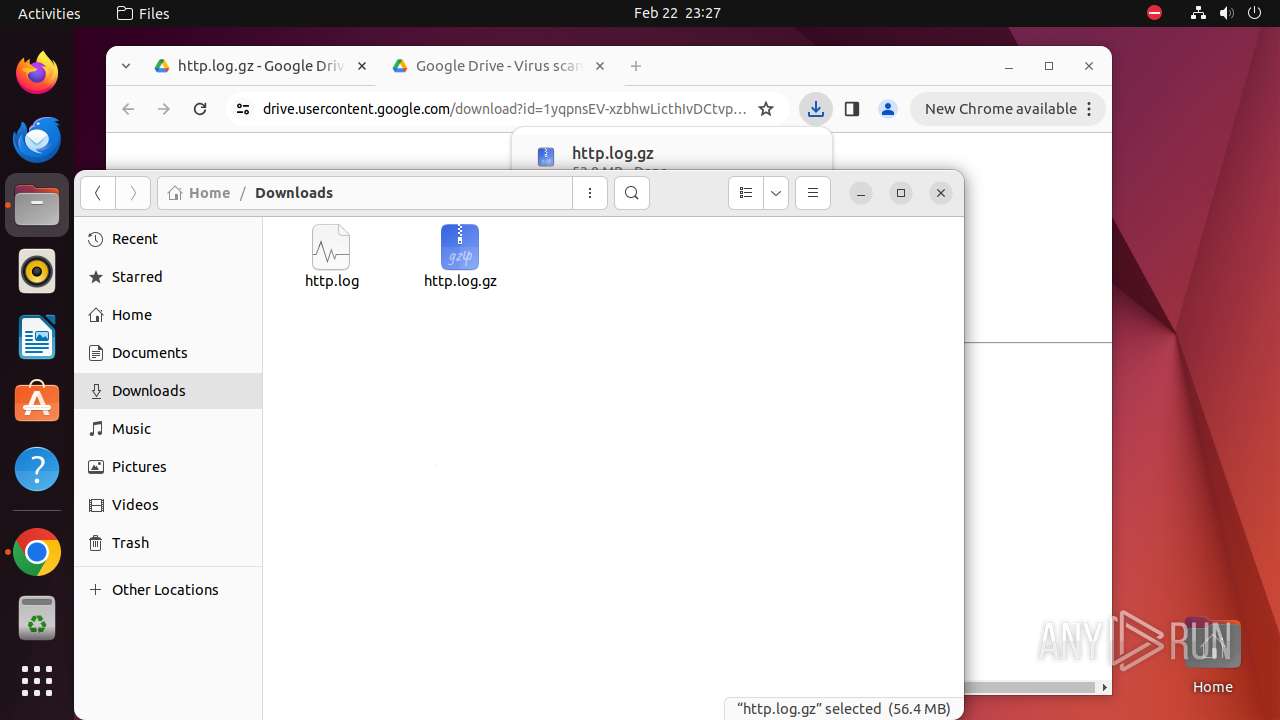
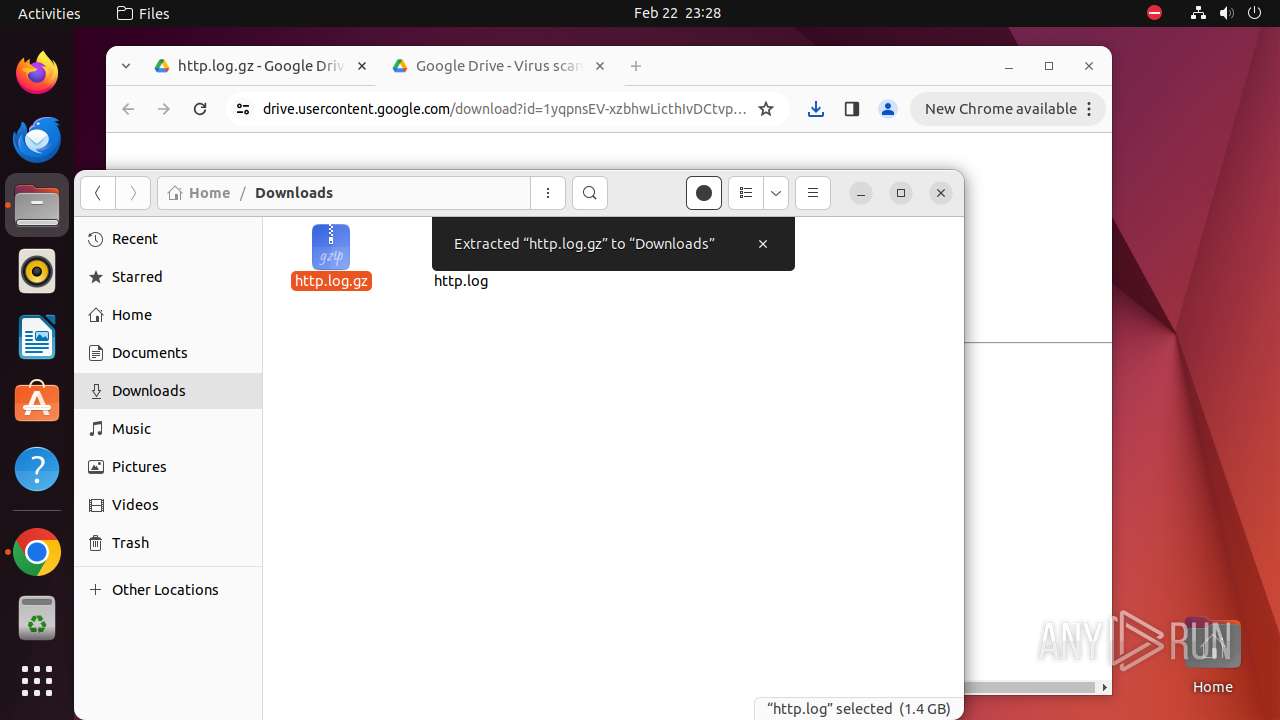
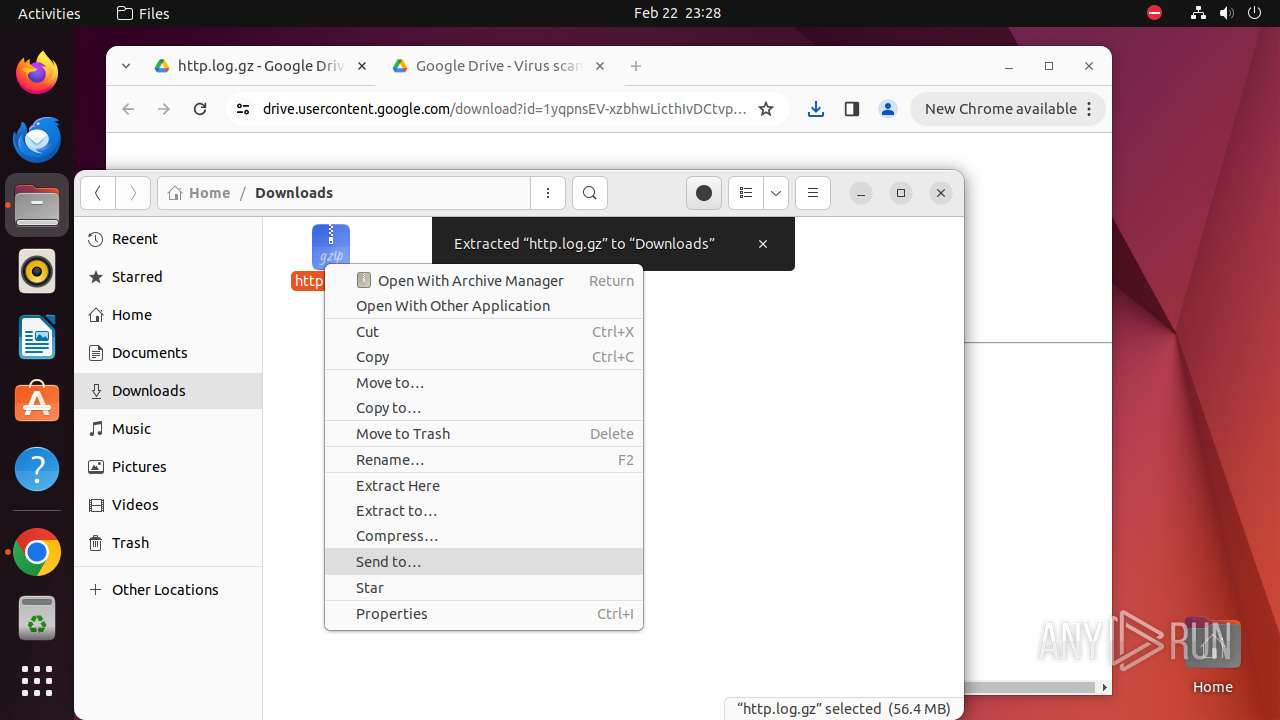
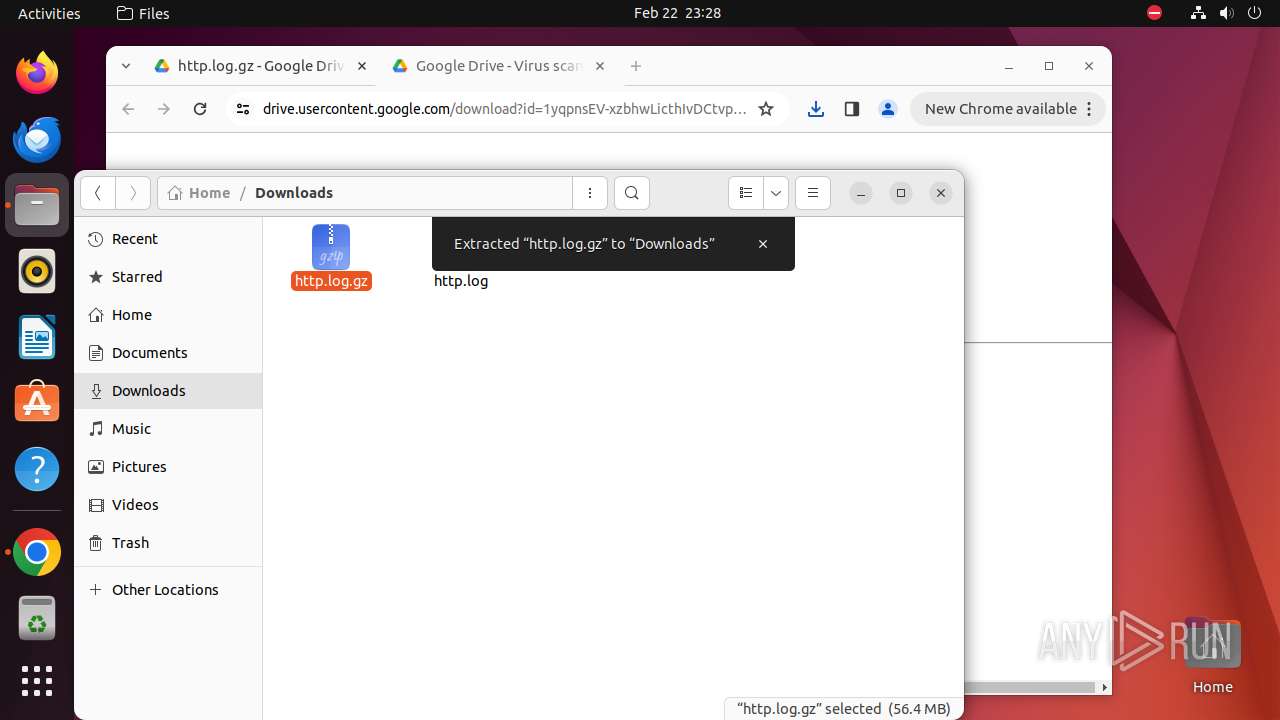
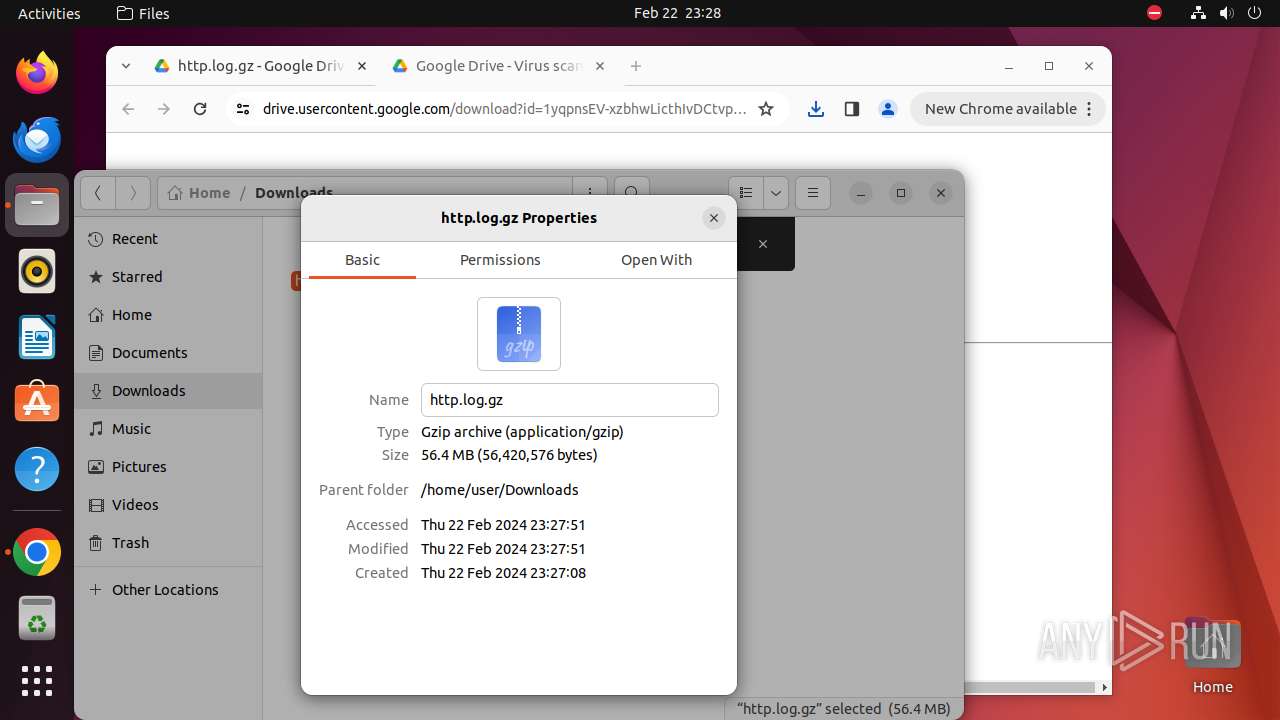
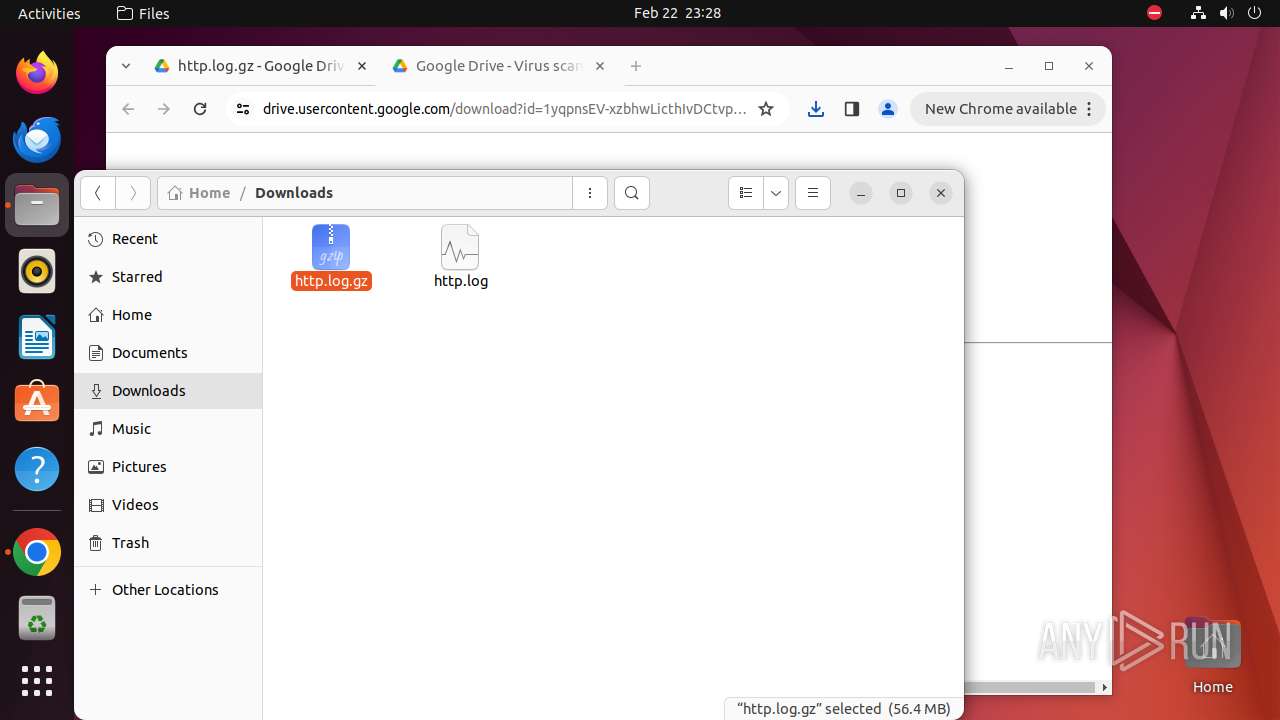
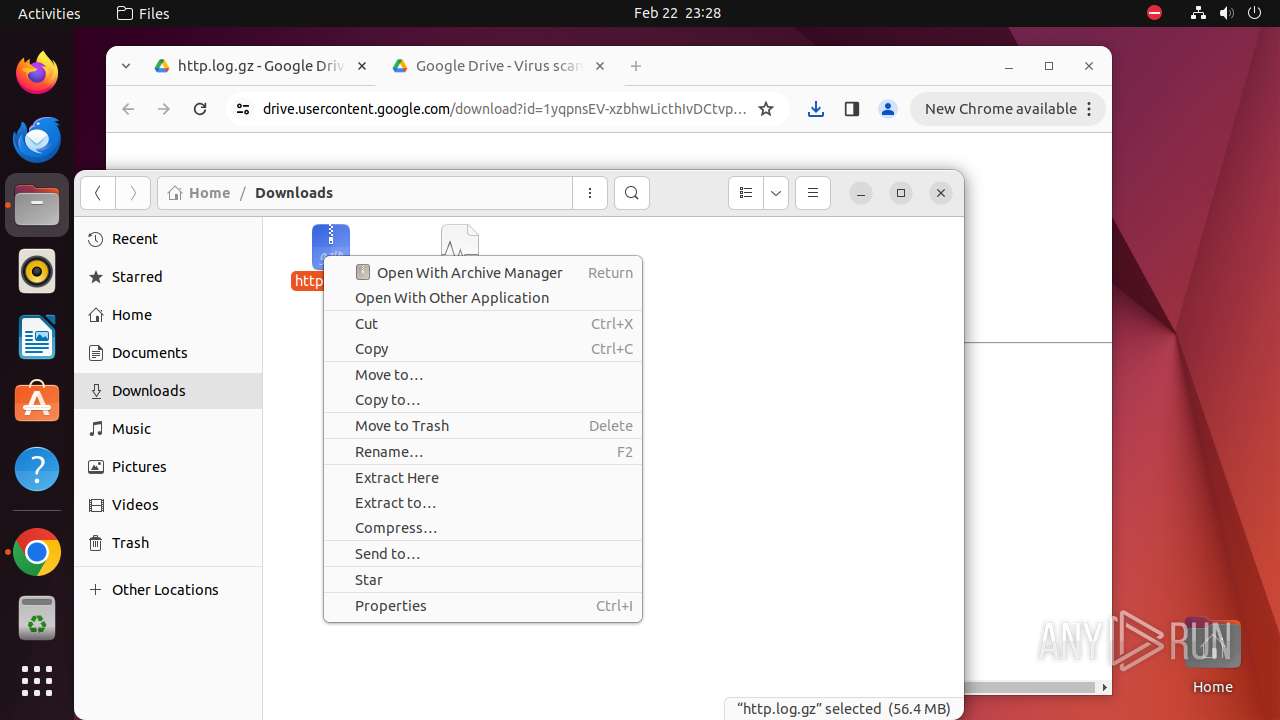
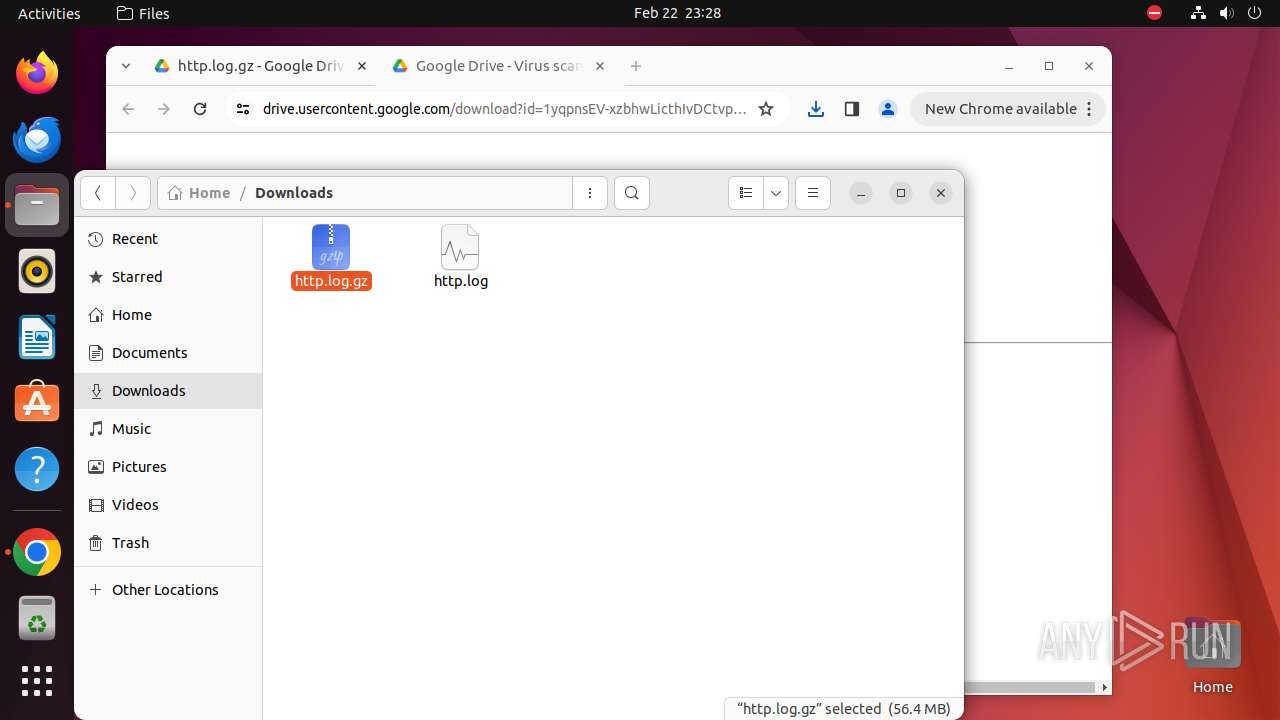
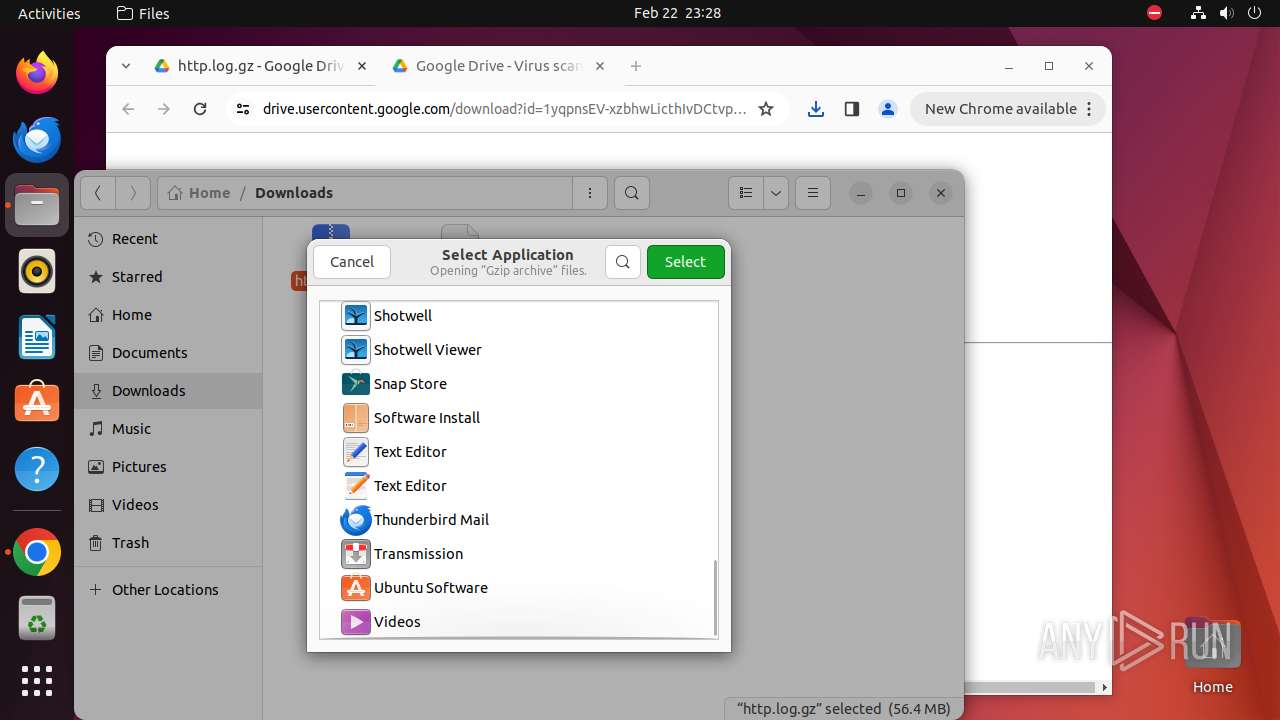
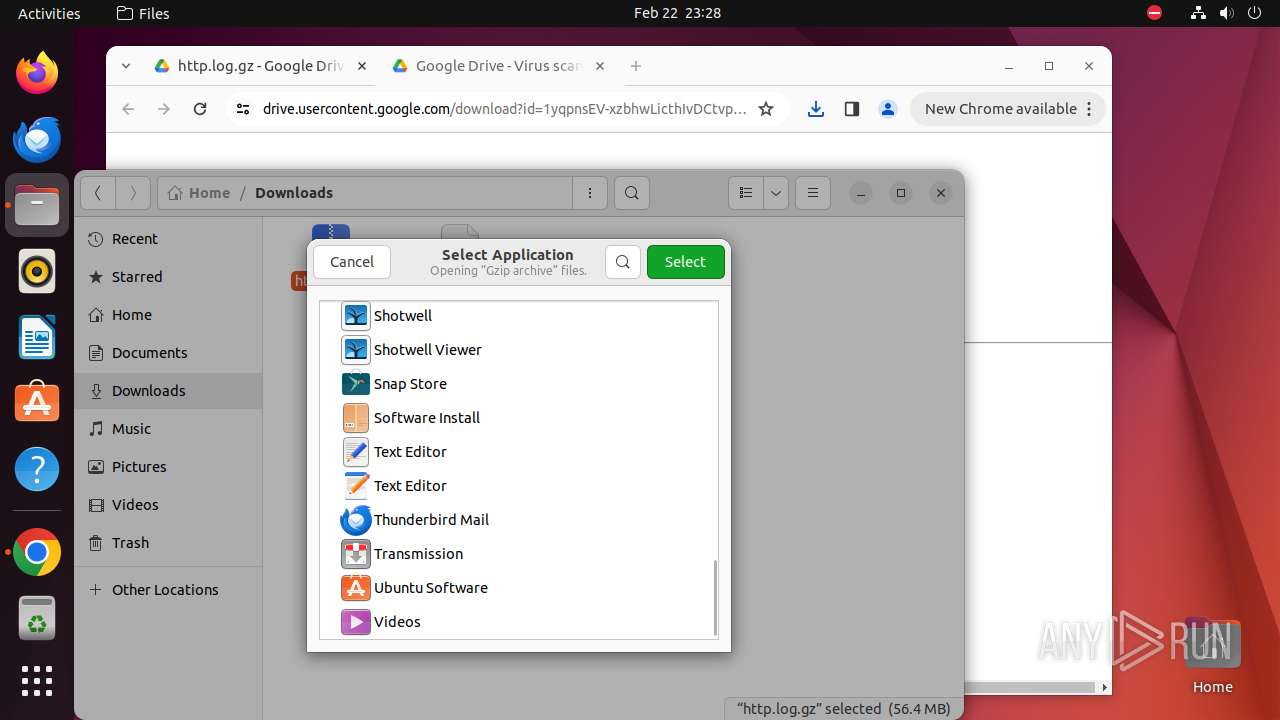
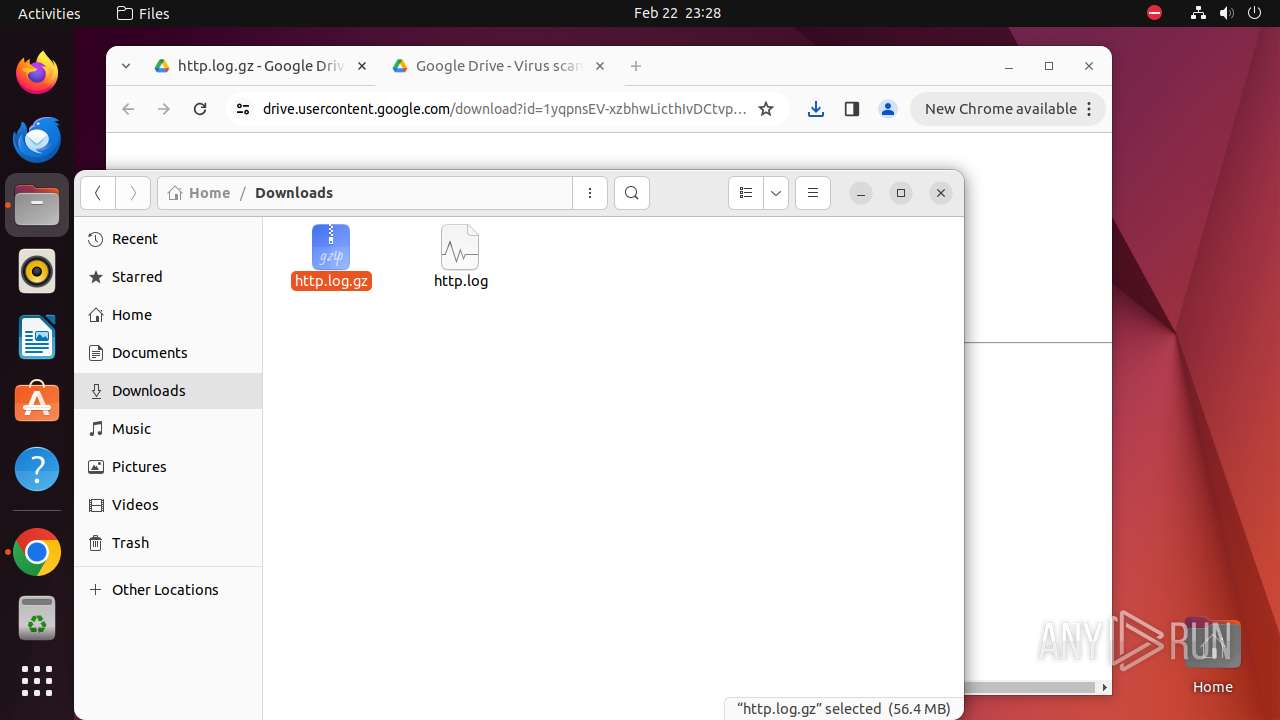
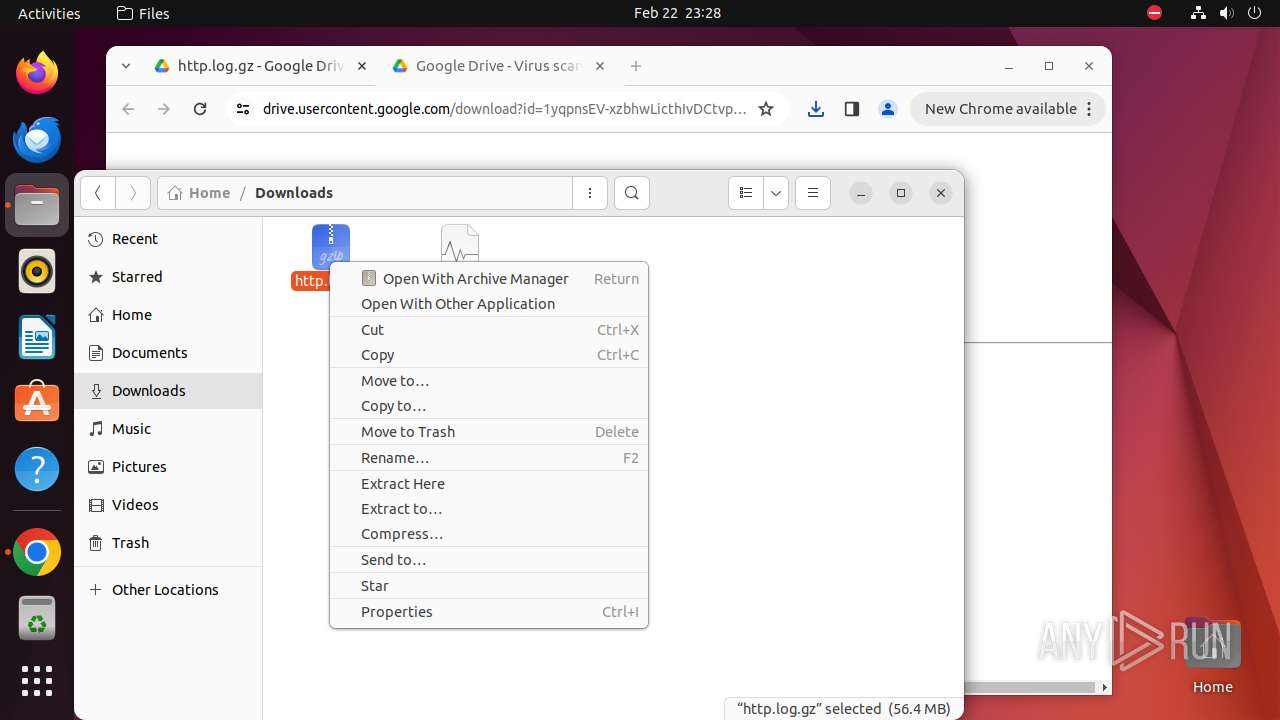
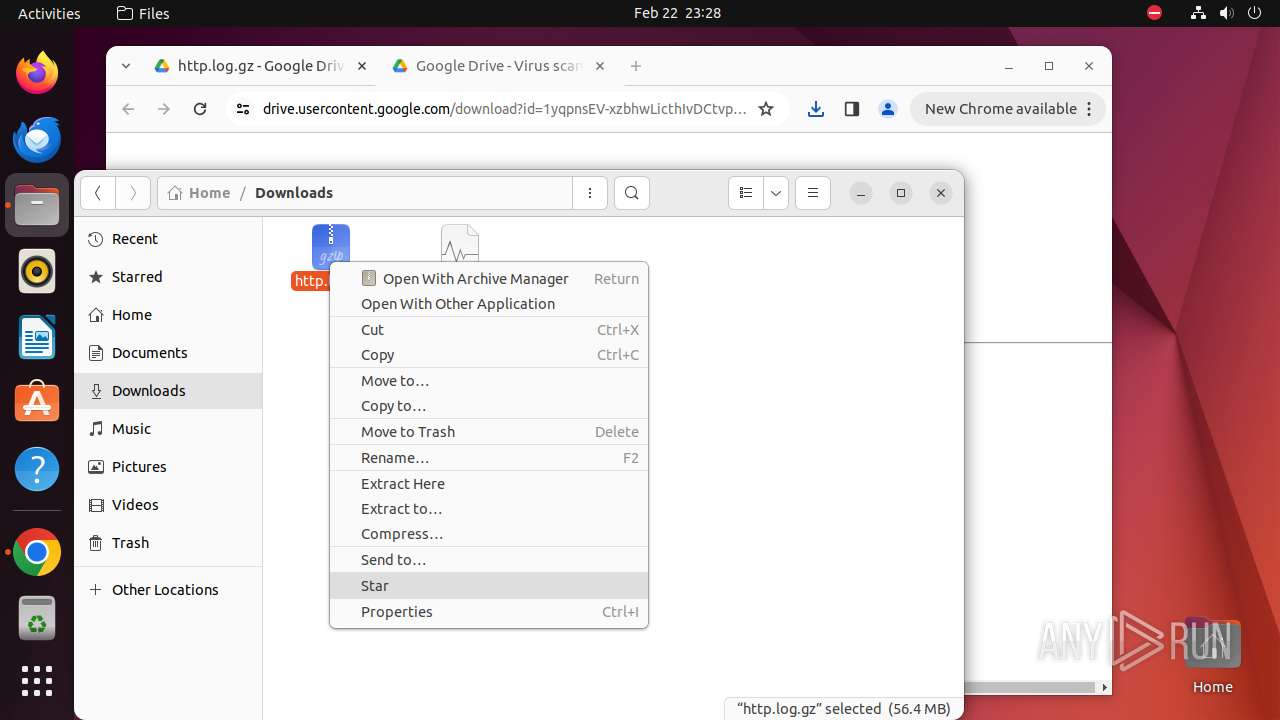
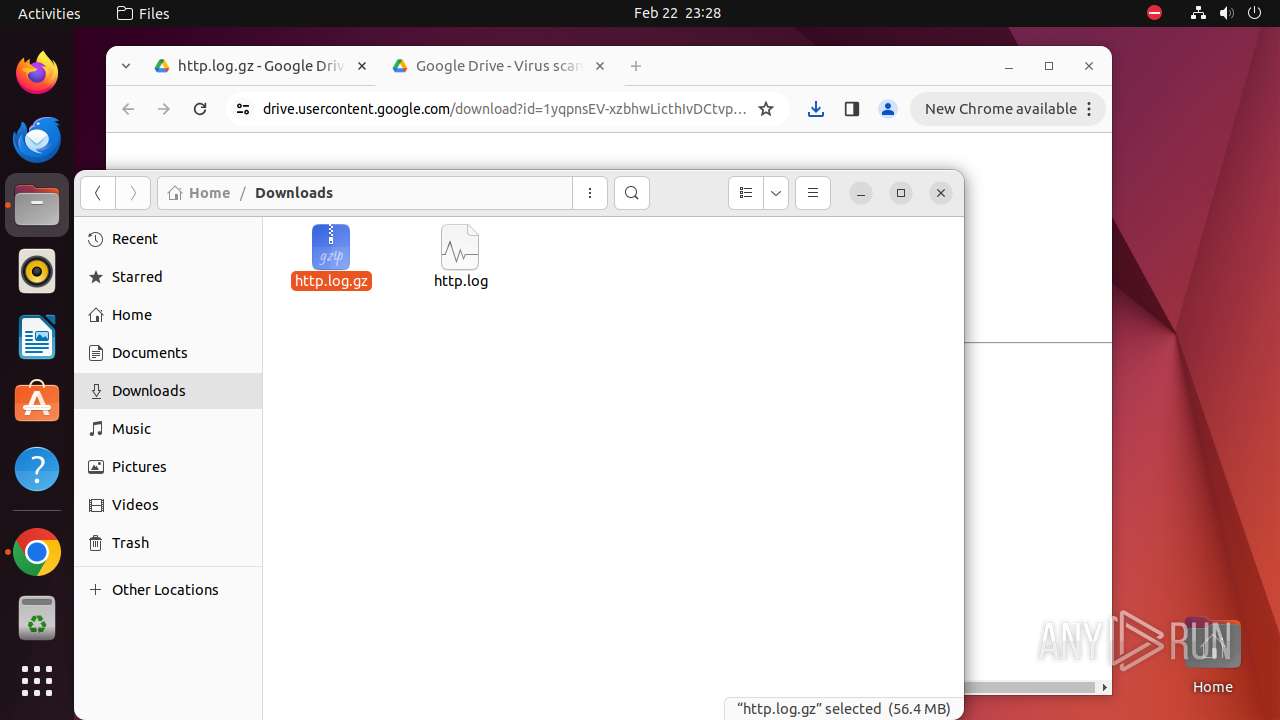
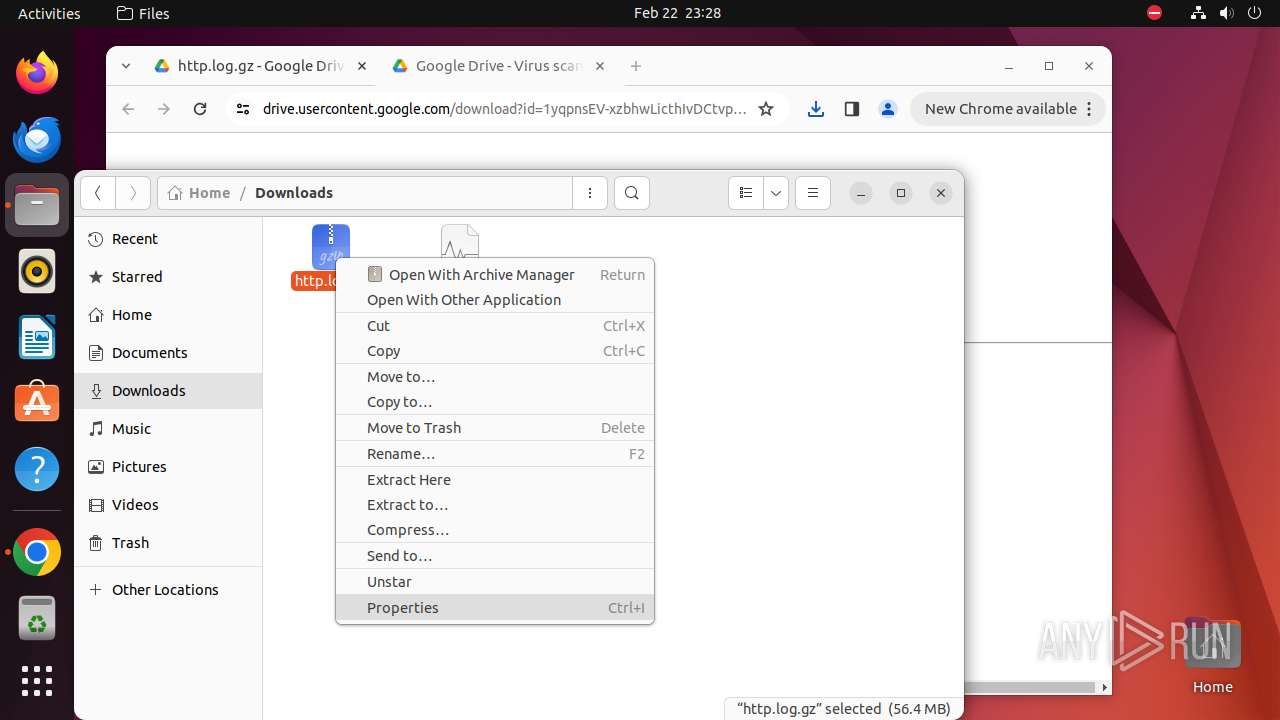
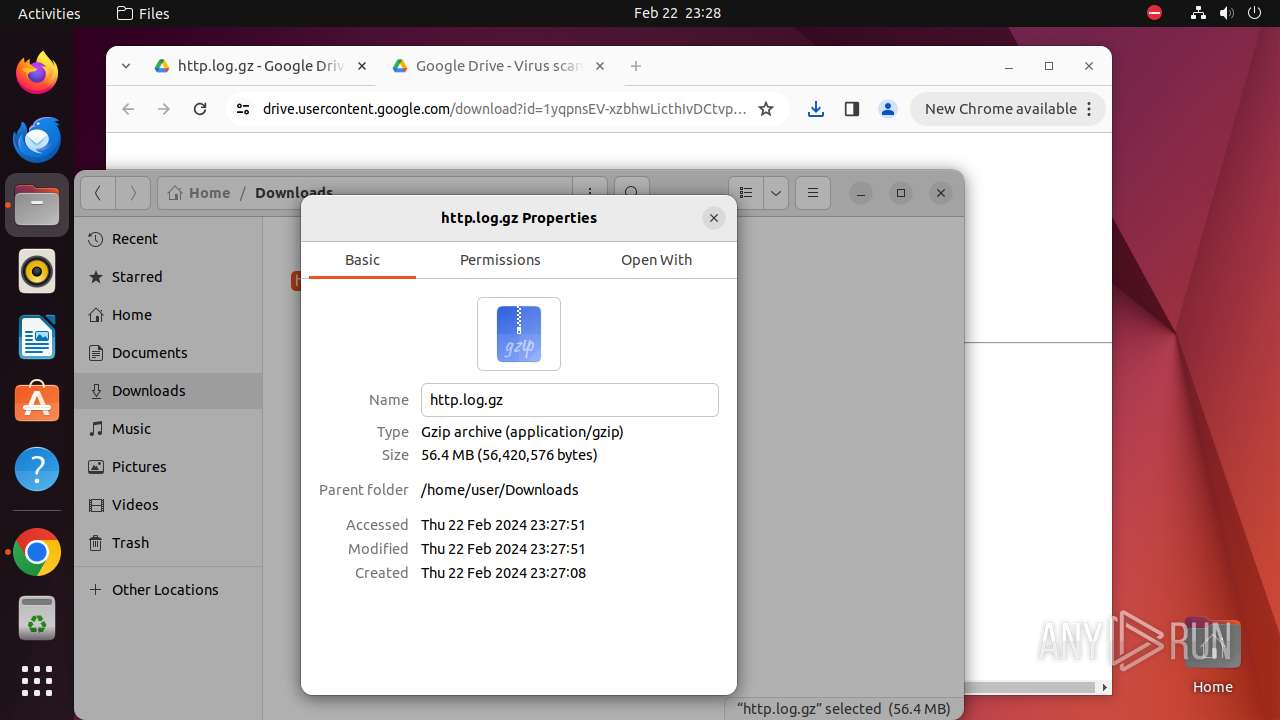
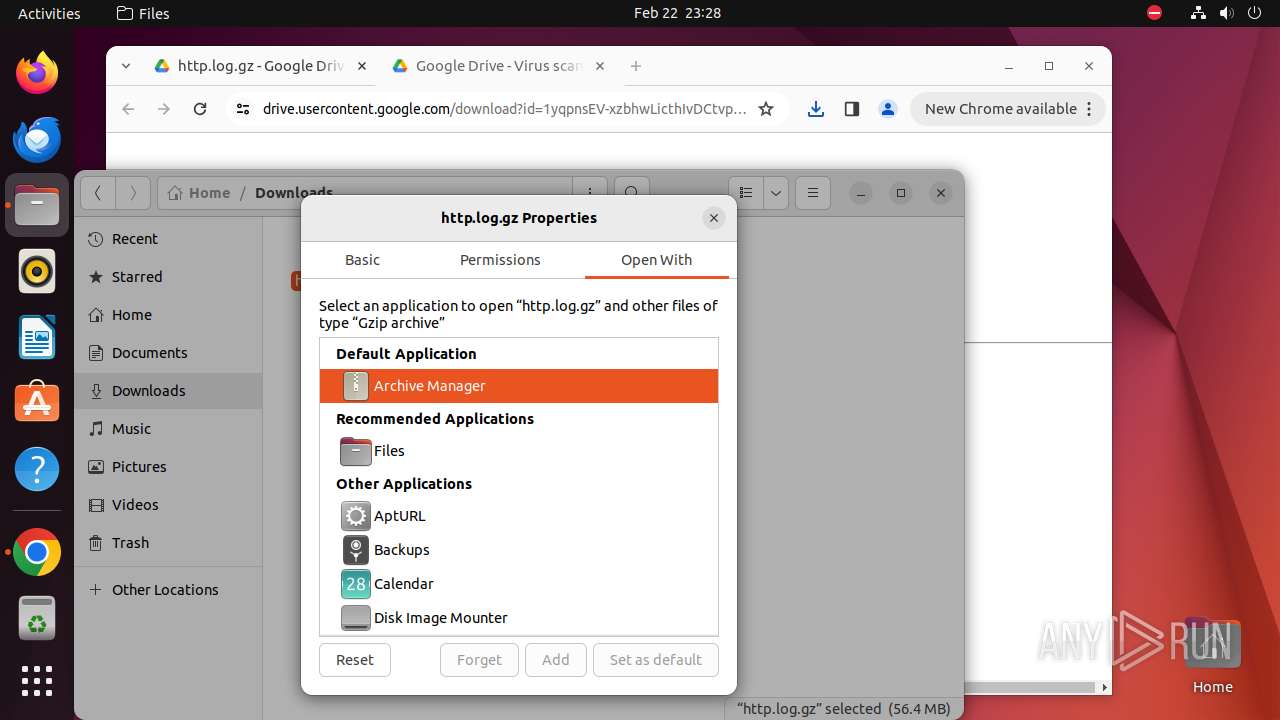
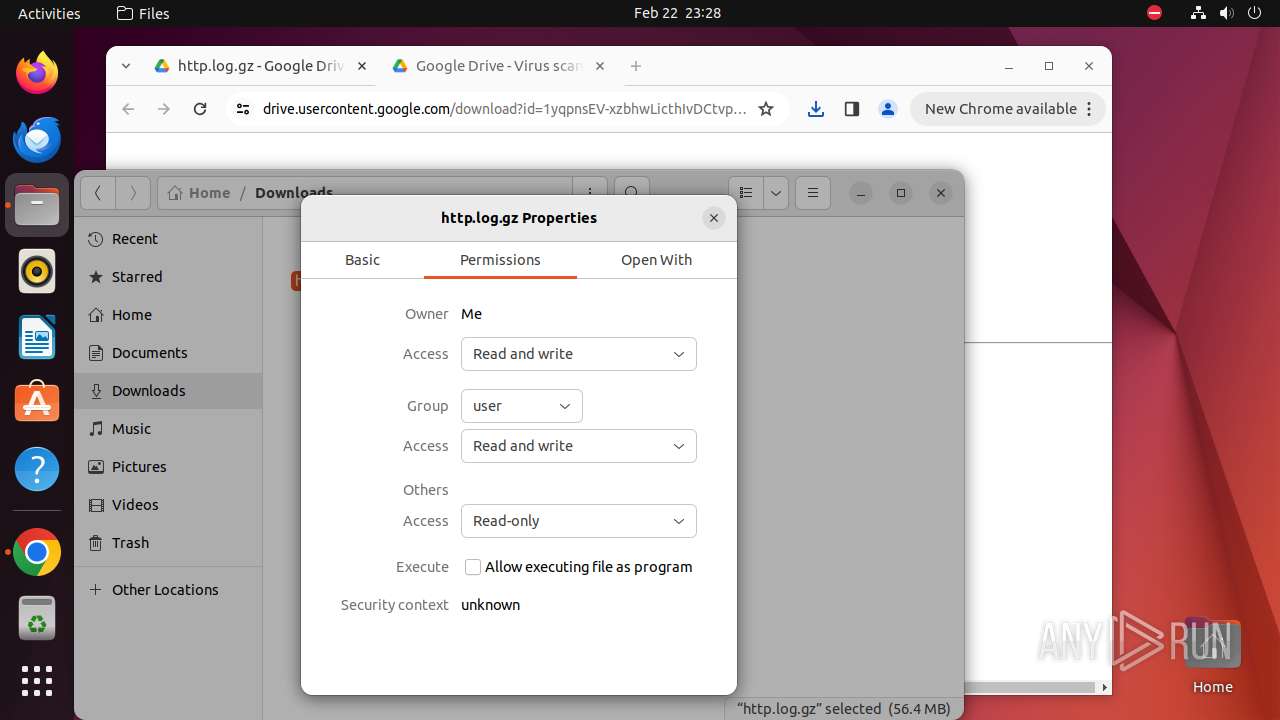
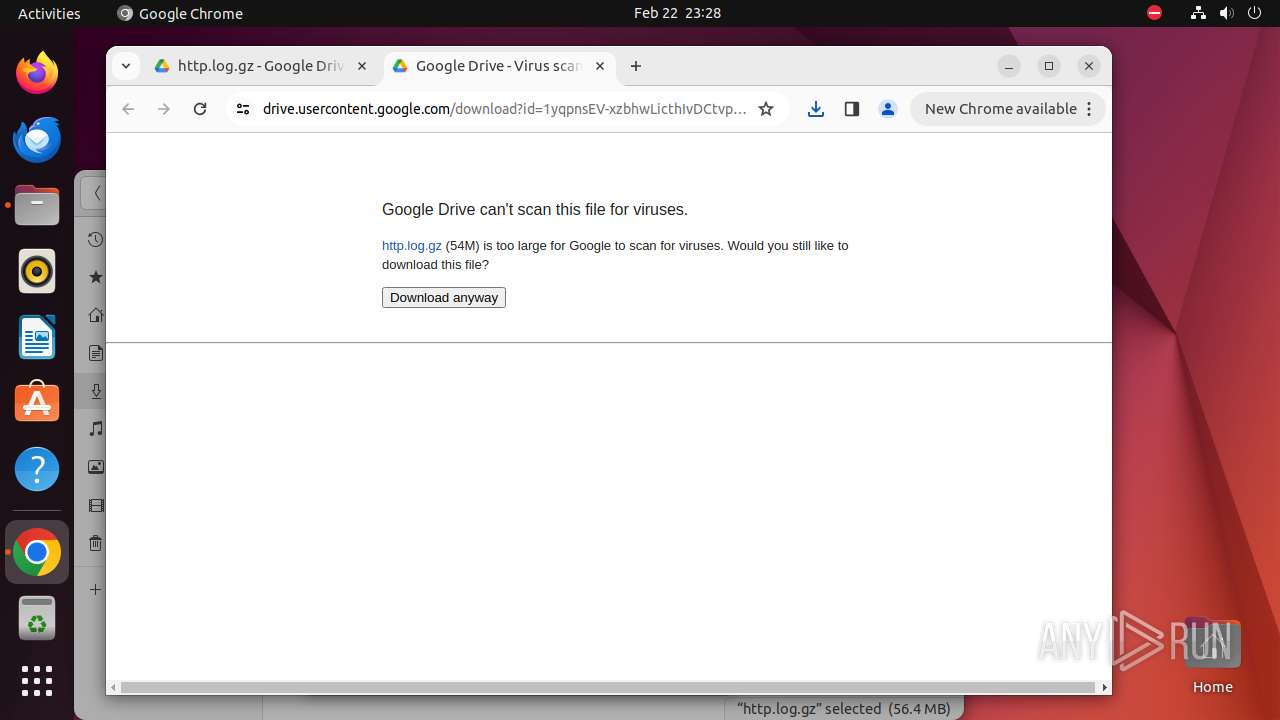
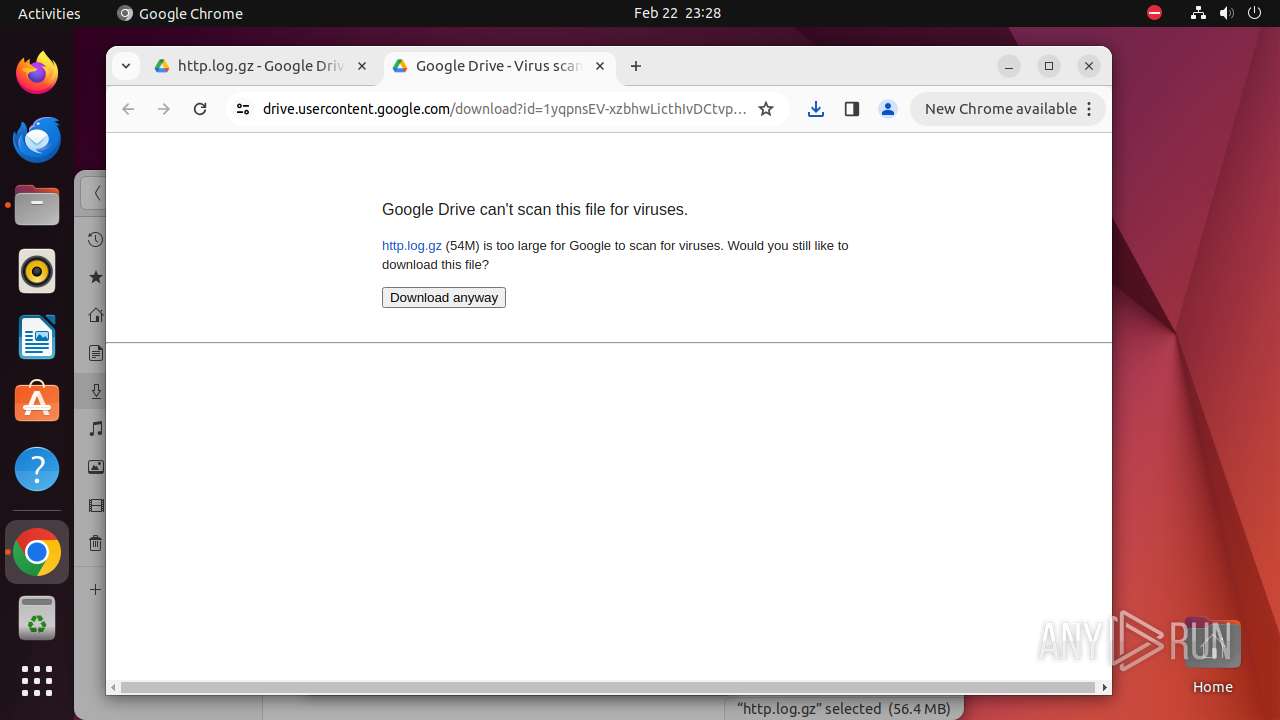
| download: | /file/d/1yqpnsEV-xzbhwLicthIvDCtvpdYhU-oh/view |
| Full analysis: | https://app.any.run/tasks/27d75874-6d04-4f71-a457-2c45e4d613a4 |
| Verdict: | Malicious activity |
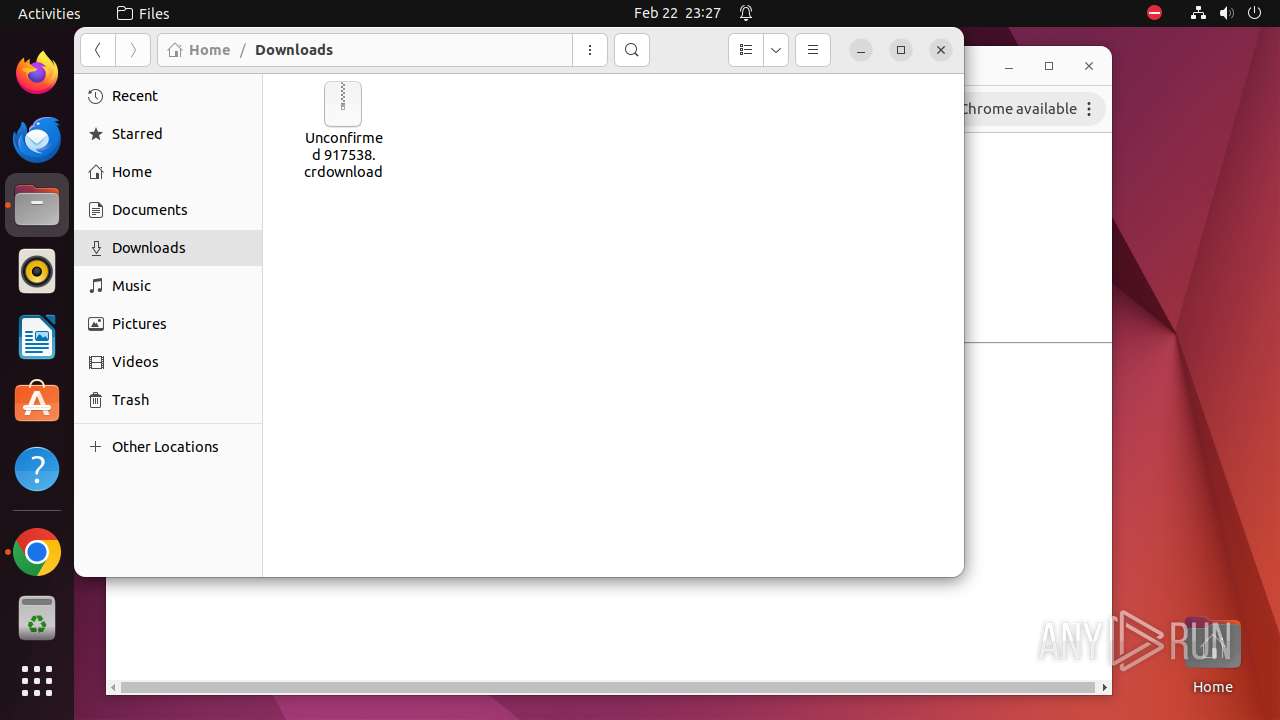
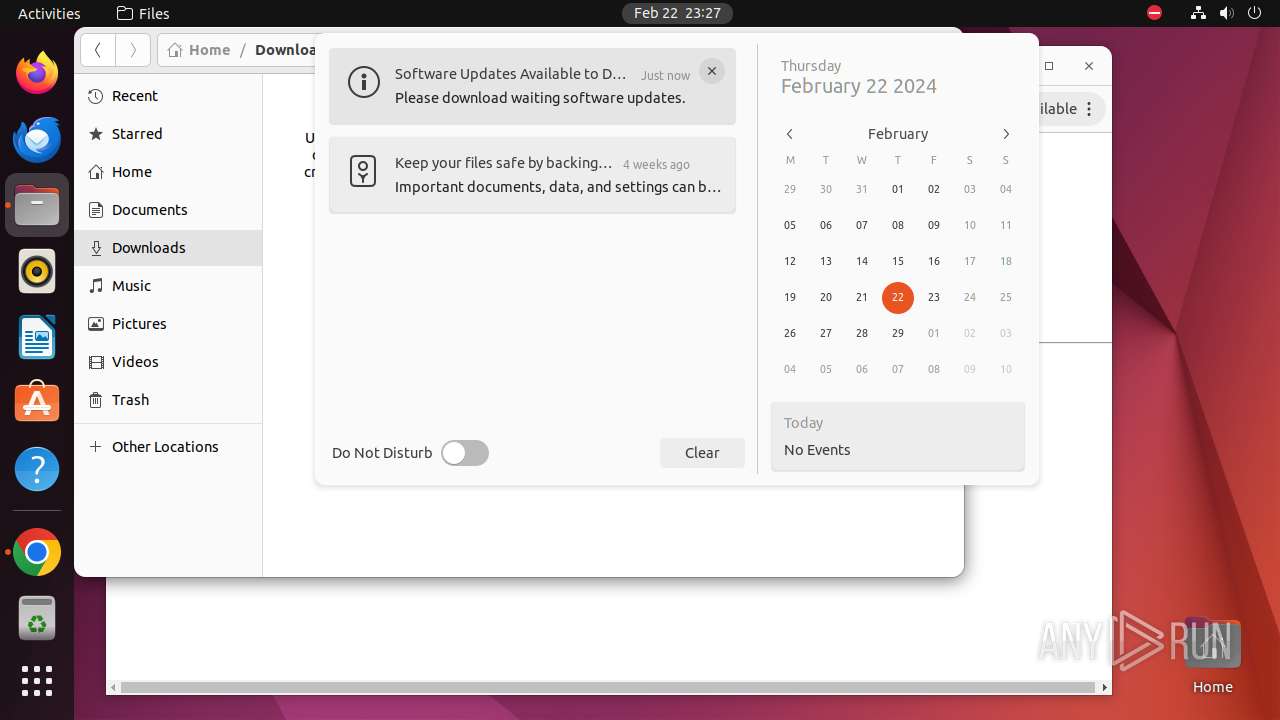
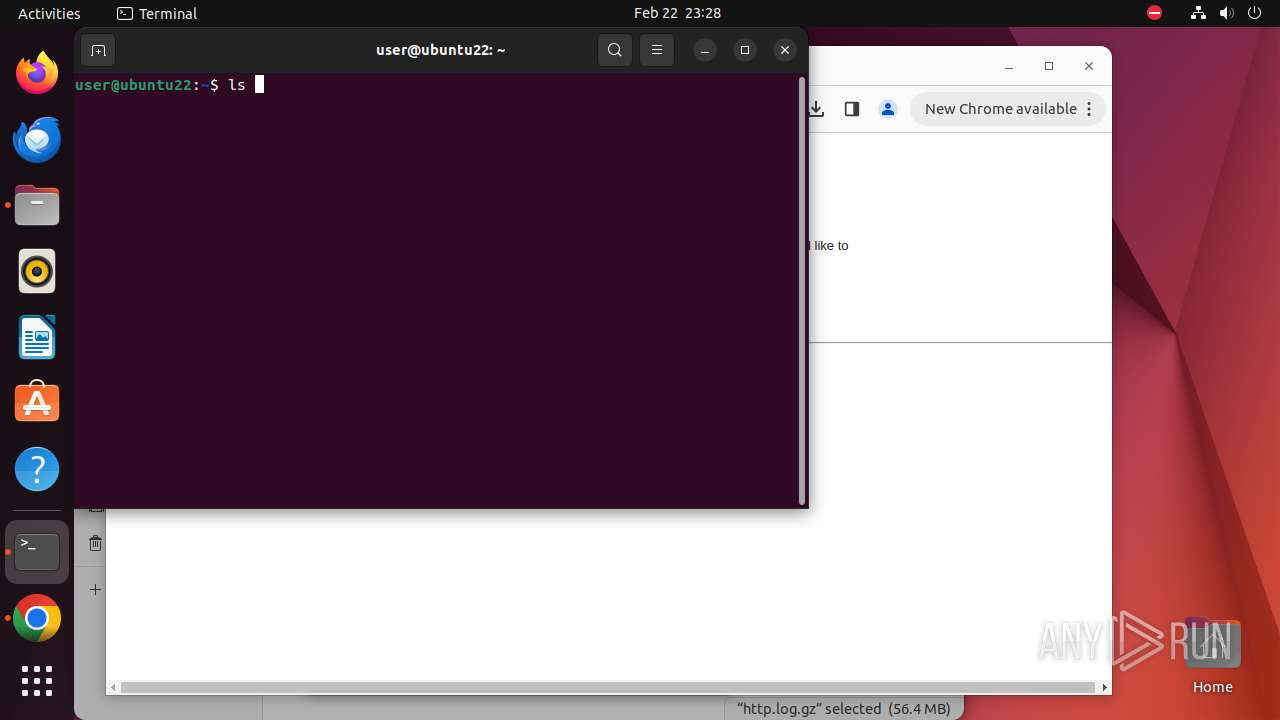
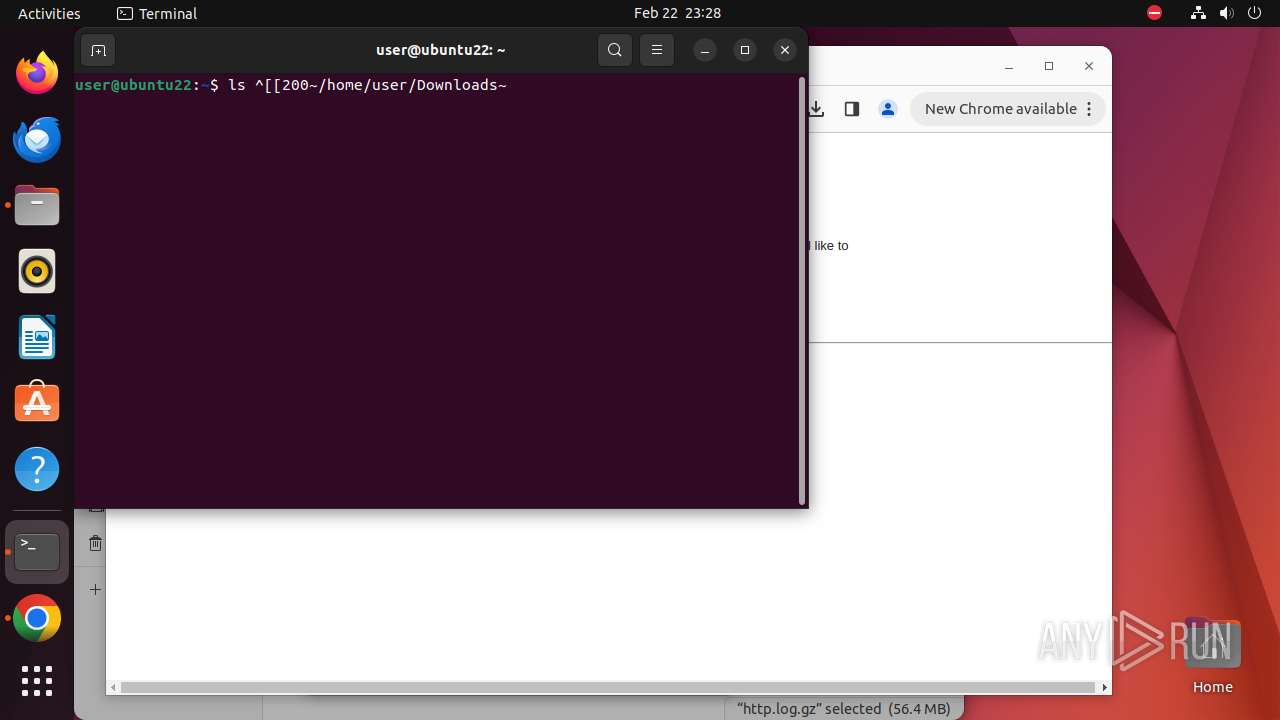
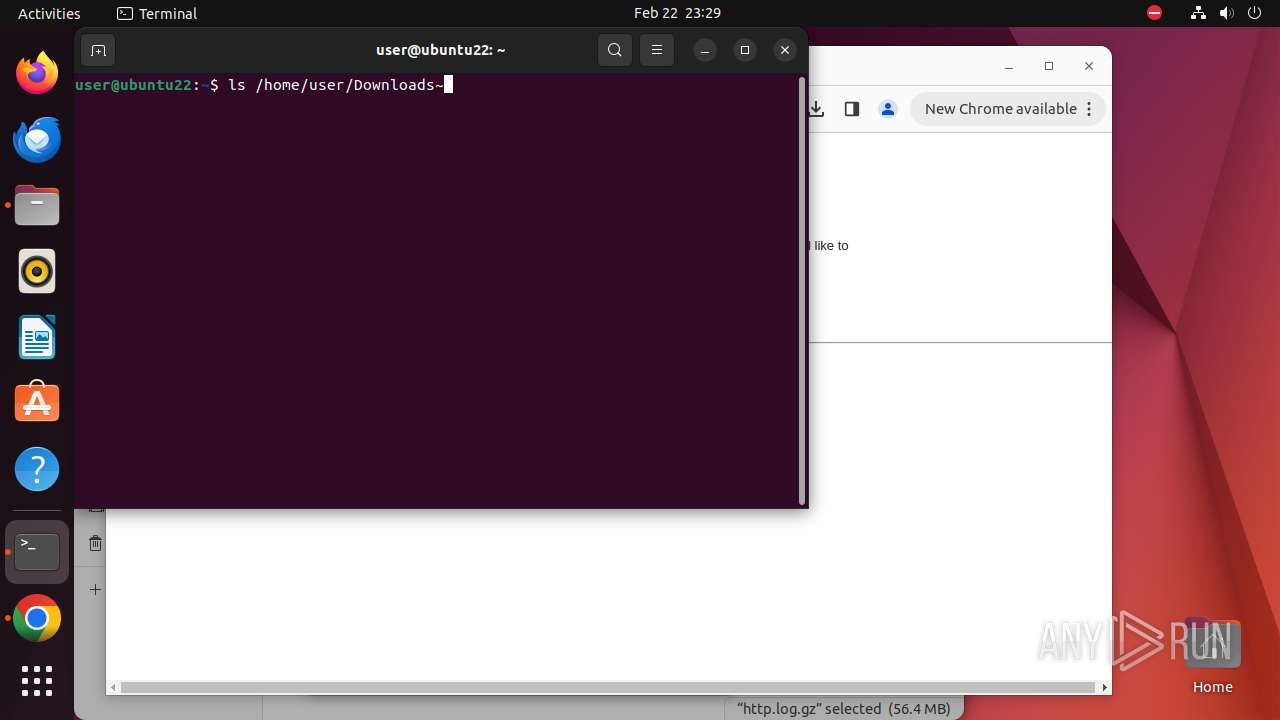
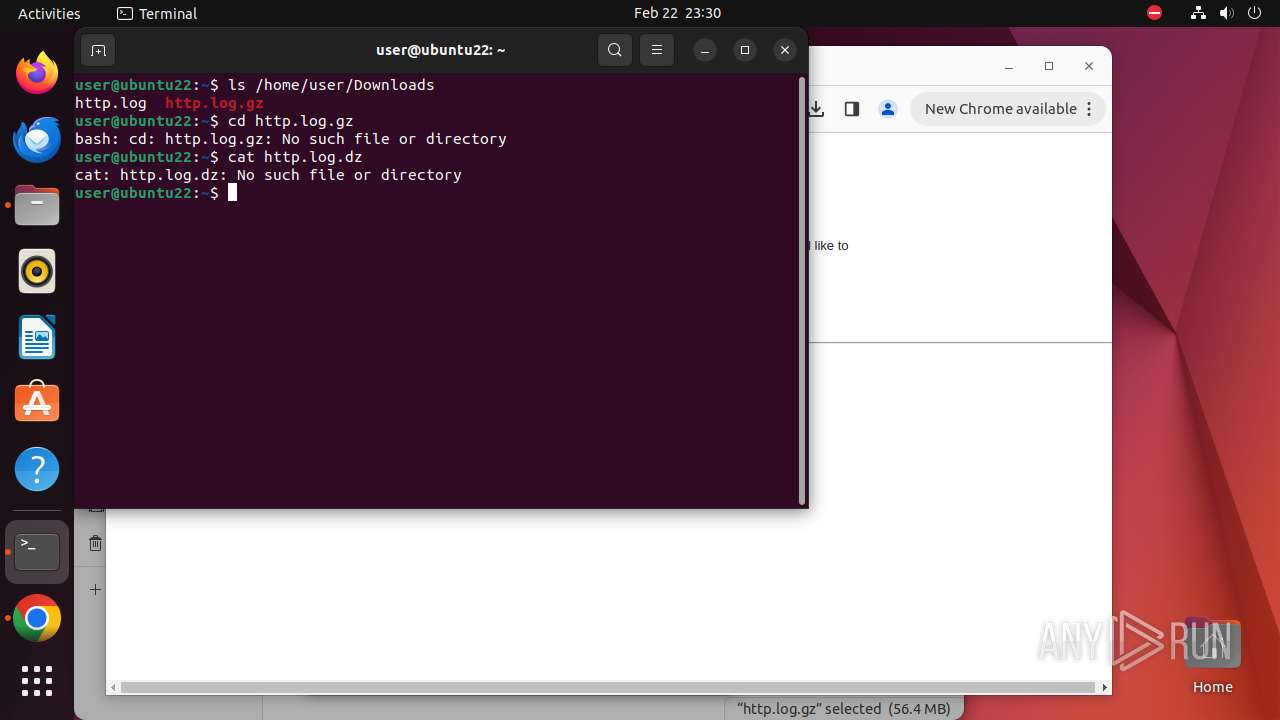
| Analysis date: | February 22, 2024, 23:26:50 |
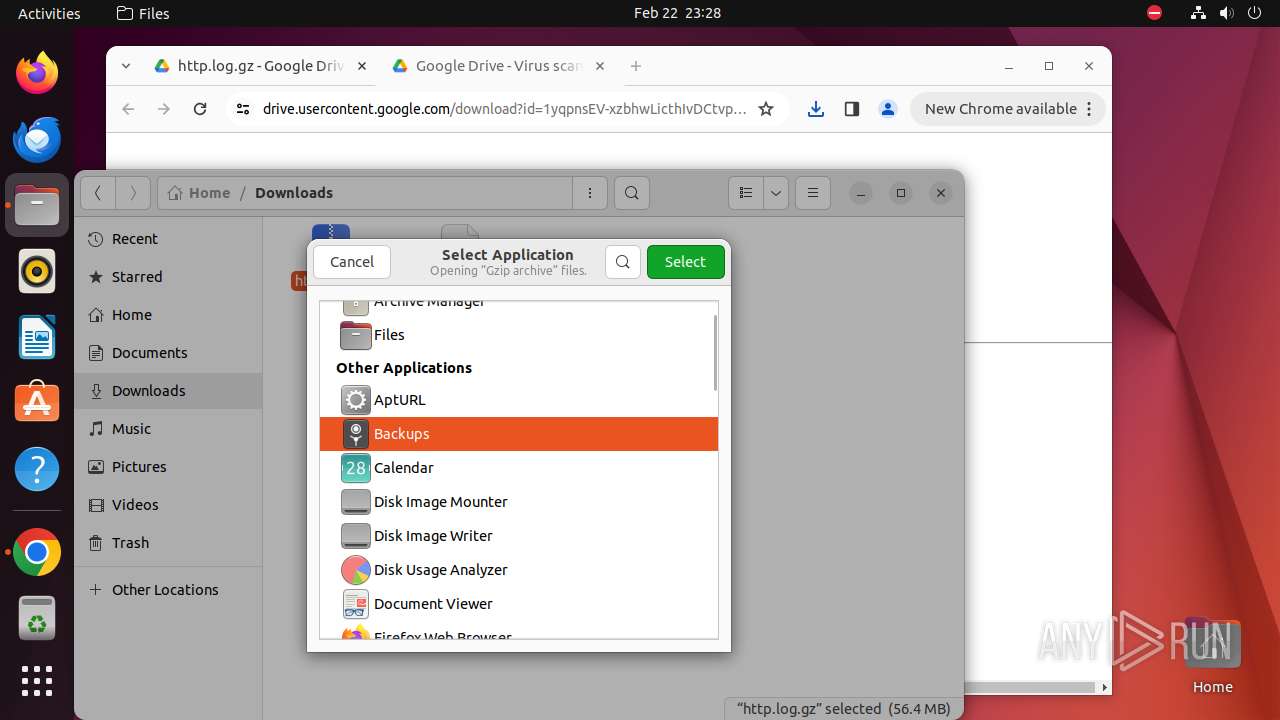
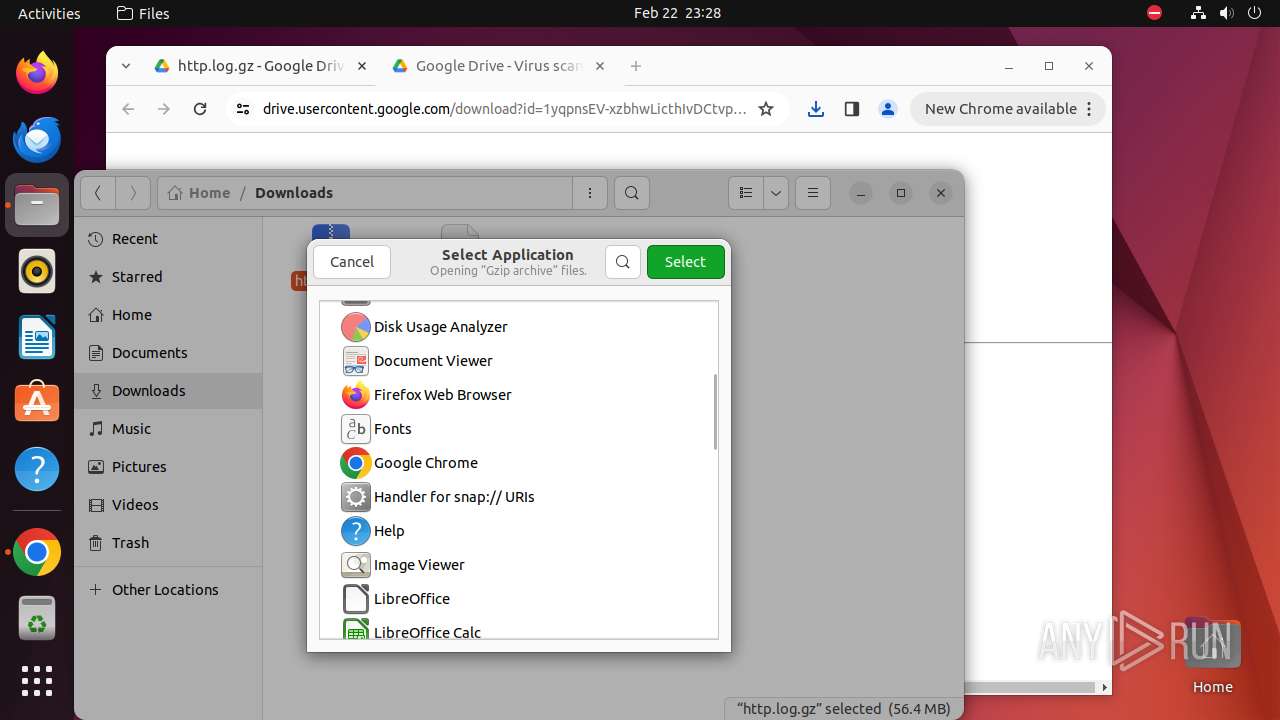
| OS: | Ubuntu 22.04.2 |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines (20886) |
| MD5: | 3868444F1FE12852D48A0688C9063AB8 |
| SHA1: | 2157A51571B81990F753A8D4439BA2792B6D259A |
| SHA256: | 586FB8069FFDFBF68BE1F7ADAA789DCAF3F597F953B5BD0543564C63A02EB4B5 |
| SSDEEP: | 1536:lS9VoTkYbvYbpD1F96DrHhkTPuMetFjWR+1YWBA:lIWejuMet8WS |
MALICIOUS
No malicious indicators.SUSPICIOUS
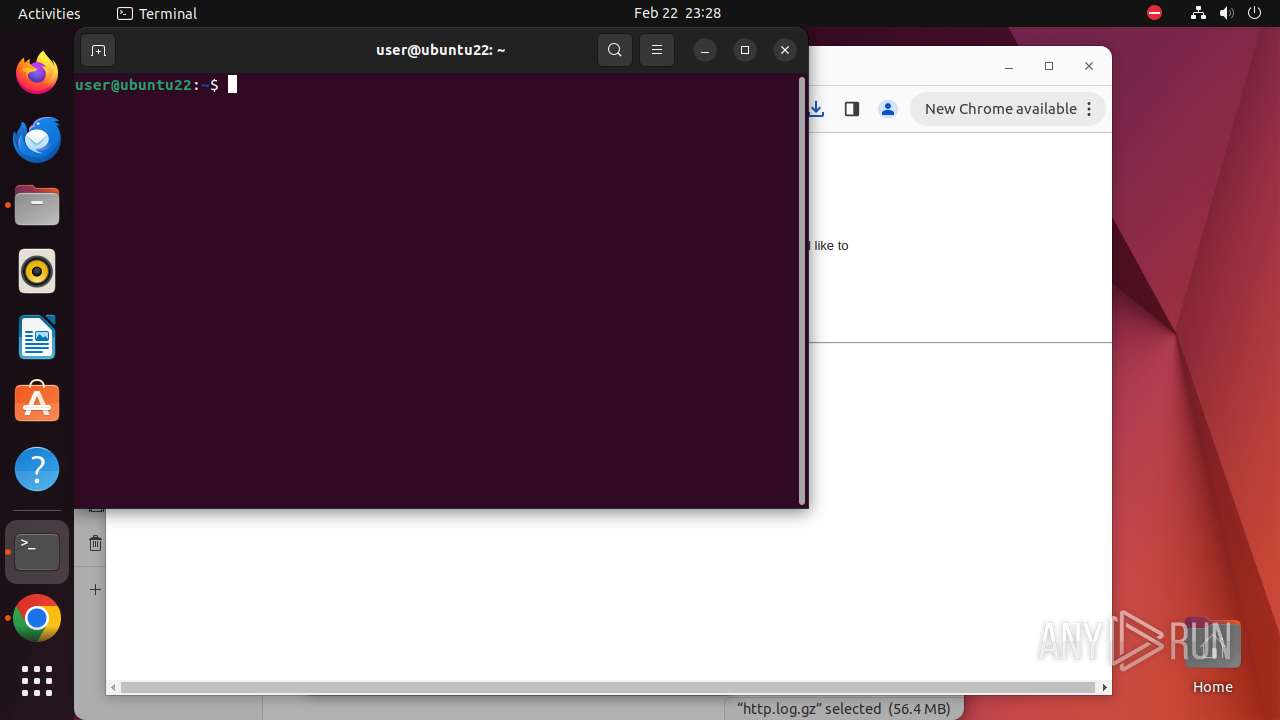
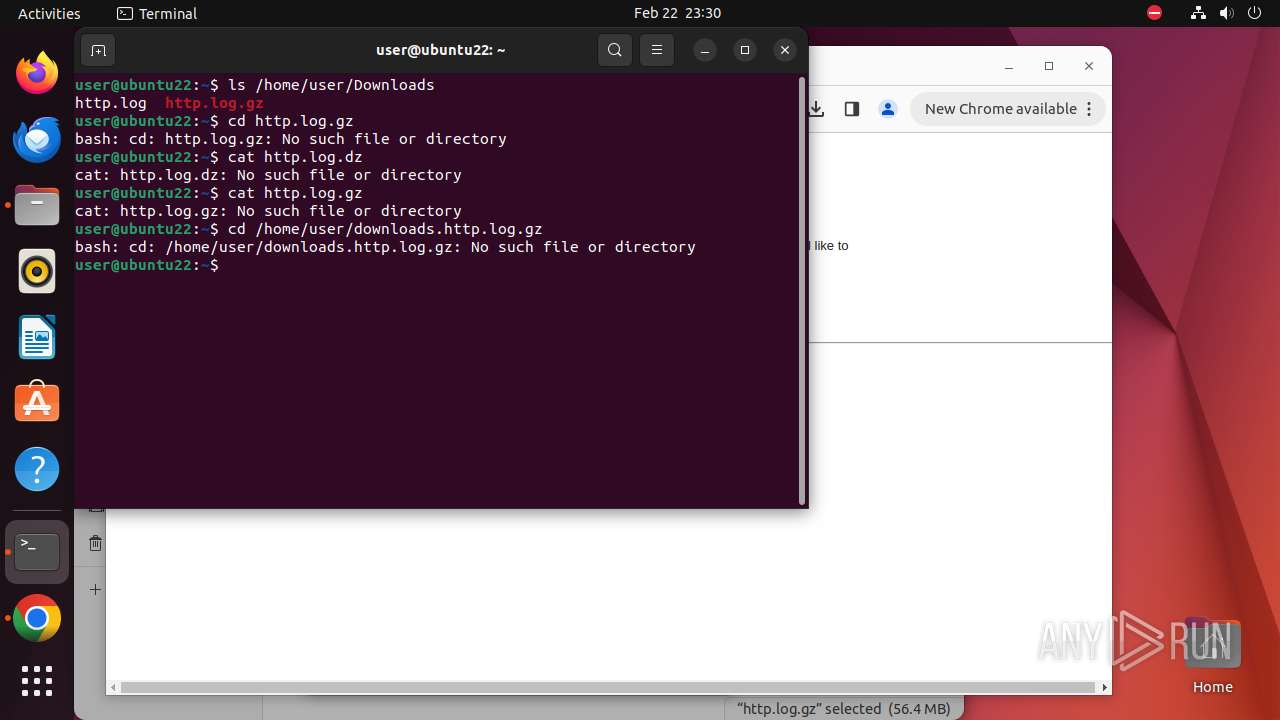
Executes commands using command-line interpreter
- gnome-terminal-server (PID: 8277)
- cron (PID: 8314)
Checks DMI information (probably VM detection)
- systemd-hostnamed (PID: 8198)
Checks the user who created the process
- cron (PID: 8314)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
Total processes
316
Monitored processes
97
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
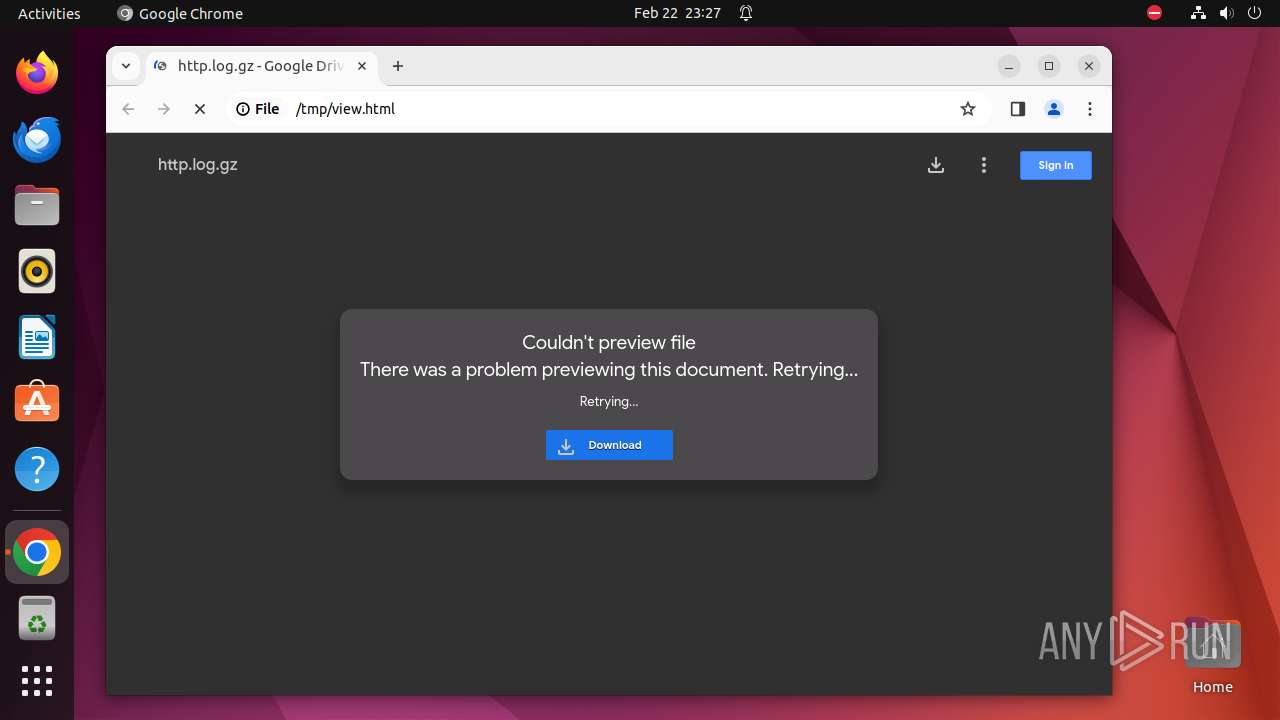
| 7937 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome \"/tmp/view\.html\" " | /bin/sh | — | any-guest-agent |
User: root Integrity Level: UNKNOWN | ||||
| 7938 | sudo -iu user google-chrome /tmp/view.html | /usr/bin/sudo | — | sh |
User: root Integrity Level: UNKNOWN | ||||
| 7939 | /usr/bin/google-chrome /tmp/view.html | /opt/google/chrome/chrome | — | sudo |
User: user Integrity Level: UNKNOWN | ||||
| 7940 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7941 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7942 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7943 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7944 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 7945 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 7946 | /opt/google/chrome/chrome | — | chrome | |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7939 | chrome | /7939/fd/63 | — | |
MD5:— | SHA256:— | |||
| 7939 | chrome | /home/user/.config/google-chrome/BrowserMetrics/BrowserMetrics-65D7D844-1F03.pma | — | |
MD5:— | SHA256:— | |||
| 7939 | chrome | /.com.google.Chrome.JynwbU | — | |
MD5:— | SHA256:— | |||
| 7939 | chrome | /.com.google.Chrome.Nu7KvF | — | |
MD5:— | SHA256:— | |||
| 7939 | chrome | /home/user/.config/google-chrome/Default/Local Storage/leveldb/LOG | — | |
MD5:— | SHA256:— | |||
| 7939 | chrome | /home/user/.config/google-chrome/Default/Site Characteristics Database/LOG | — | |
MD5:— | SHA256:— | |||
| 7939 | chrome | /home/user/.config/google-chrome/Default/commerce_subscription_db/LOG | — | |
MD5:— | SHA256:— | |||
| 7939 | chrome | /home/user/.config/google-chrome/Default/discounts_db/LOG | — | |
MD5:— | SHA256:— | |||
| 7939 | chrome | /home/user/.config/google-chrome/Default/parcel_tracking_db/LOG | — | |
MD5:— | SHA256:— | |||
| 7939 | chrome | /home/user/.config/google-chrome/Default/chrome_cart_db/LOG | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
59
DNS requests
83
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/achbl36stp77xmtl7bf4ynoyeduq_2024.2.21.1/jflhchccmppkfebkiaminageehmchikm_2024.02.21.01_all_kngxaemc3fjbnntpm2j46wzyse.crx3 | unknown | text | 37 b | unknown |
— | — | GET | 200 | 216.58.212.142:80 | http://dl.google.com/release2/chrome_component/achbl36stp77xmtl7bf4ynoyeduq_2024.2.21.1/jflhchccmppkfebkiaminageehmchikm_2024.02.21.01_all_kngxaemc3fjbnntpm2j46wzyse.crx3 | unknown | binary | 7.79 Kb | unknown |
— | — | GET | 200 | 194.9.25.143:80 | http://r3---sn-5uh5o-f5fk.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx?cms_redirect=yes&mh=kX&mip=45.138.16.76&mm=28&mn=sn-5uh5o-f5fk&ms=nvh&mt=1708644021&mv=m&mvi=3&pl=24&rmhost=r2---sn-5uh5o-f5fk.gvt1.com&shardbypass=sd&smhost=r5---sn-5uh5o-f5f6.gvt1.com | unknown | binary | 3.07 Kb | unknown |
— | — | GET | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | text | 37 b | unknown |
— | — | GET | 302 | 142.250.185.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | html | 600 b | unknown |
— | — | GET | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/gonpemdgkjcecdgbnaabipppbmgfggbe/1.7e7996864a74a4b8db2b59c559f924f321668848edbcb85386212a4901ef0e6e/1.48fecfa3c6f59eb6c34fdd5e8f19e0678699e2f27dc8ebfa7025c246d4575c68/4f40609d14bbd0e6dbc34e28e63286a878e52c3c2e623faa62306d69c2705d63.puff | unknown | text | 37 b | unknown |
— | — | GET | 204 | 185.125.190.48:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | unknown |
— | — | GET | 200 | 216.58.212.142:80 | http://dl.google.com/release2/chrome_component/a7cbhm53ik274vwlrk6bjaq5su_2024.2.14.0/gonpemdgkjcecdgbnaabipppbmgfggbe_2024.02.14.00_all_k7tvzi4dxufc2ebisykc3i47ni.crx3 | unknown | binary | 6.17 Kb | unknown |
— | — | GET | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/a7cbhm53ik274vwlrk6bjaq5su_2024.2.14.0/gonpemdgkjcecdgbnaabipppbmgfggbe_2024.02.14.00_all_k7tvzi4dxufc2ebisykc3i47ni.crx3 | unknown | text | 37 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 156.146.33.141:443 | — | Datacamp Limited | DE | unknown |
— | — | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 239.255.255.250:1900 | — | — | — | unknown |
— | — | 142.250.181.227:443 | clientservices.googleapis.com | GOOGLE | US | unknown |
— | — | 74.125.206.84:443 | accounts.google.com | GOOGLE | US | unknown |
— | — | 142.250.186.170:443 | fonts.googleapis.com | GOOGLE | US | unknown |
— | — | 142.250.186.35:443 | www.gstatic.com | GOOGLE | US | unknown |
— | — | 142.250.184.195:443 | fonts.gstatic.com | GOOGLE | US | unknown |
— | — | 142.250.186.110:443 | drive.google.com | GOOGLE | US | unknown |
— | — | 142.250.181.238:443 | play.google.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
drive.google.com |
| shared |
play.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
content.googleapis.com |
| whitelisted |